Internet Explorer derives a cache filename from a URL, and then in certain circumstances, uses the extension of the resulting file to determine the content type of the data, ignoring the Content-Type header. More...
Static Public Member Functions | |
| static | areServerVarsBad ($vars, $extWhitelist=array()) |
| Check a subset of $_SERVER (or the whole of $_SERVER if you like) to see if it indicates that the request was sent with a bad file extension. | |
| static | findIE6Extension ($url) |
| Determine what extension IE6 will infer from a certain query string. | |
| static | fixUrlForIE6 ($url, $extWhitelist=array()) |
| Returns a variant of $url which will pass isUrlExtensionBad() but has the same GET parameters, or false if it can't figure one out. | |
| static | haveUndecodedRequestUri ($serverSoftware) |
| When passed the value of $_SERVER['SERVER_SOFTWARE'], this function returns true if that server is known to have a REQUEST_URI variable with %2E not decoded to ".". | |
| static | isUrlExtensionBad ($urlPart, $extWhitelist=array()) |
| Given a right-hand portion of a URL, determine whether IE would detect a potentially harmful file extension. | |
Detailed Description
Internet Explorer derives a cache filename from a URL, and then in certain circumstances, uses the extension of the resulting file to determine the content type of the data, ignoring the Content-Type header.
This can be a problem, especially when non-HTML content is sent by MediaWiki, and Internet Explorer interprets it as HTML, exposing an XSS vulnerability.
Usually the script filename (e.g. api.php) is present in the URL, and this makes Internet Explorer think the extension is a harmless script extension. But Internet Explorer 6 and earlier allows the script extension to be obscured by encoding the dot as "%2E".
This class contains functions which help in detecting and dealing with this situation.
Checking the URL for a bad extension is somewhat complicated due to the fact that CGI doesn't provide a standard method to determine the URL. Instead it is necessary to pass a subset of $_SERVER variables, which we then attempt to use to guess parts of the URL.
Definition at line 24 of file IEUrlExtension.php.
Member Function Documentation
| static IEUrlExtension::areServerVarsBad | ( | $ | vars, |
| $ | extWhitelist = array() |
||
| ) | [static] |
Check a subset of $_SERVER (or the whole of $_SERVER if you like) to see if it indicates that the request was sent with a bad file extension.
Returns true if the request should be denied or modified, false otherwise. The relevant $_SERVER elements are:
- SERVER_SOFTWARE
- REQUEST_URI
- QUERY_STRING
- PATH_INFO
If the a variable is unset in $_SERVER, it should be unset in $vars.
- Parameters:
-
$vars A subset of $_SERVER. $extWhitelist Extensions which are allowed, assumed harmless.
- Returns:
- bool
Definition at line 42 of file IEUrlExtension.php.
Referenced by WebRequest\checkUrlExtension().

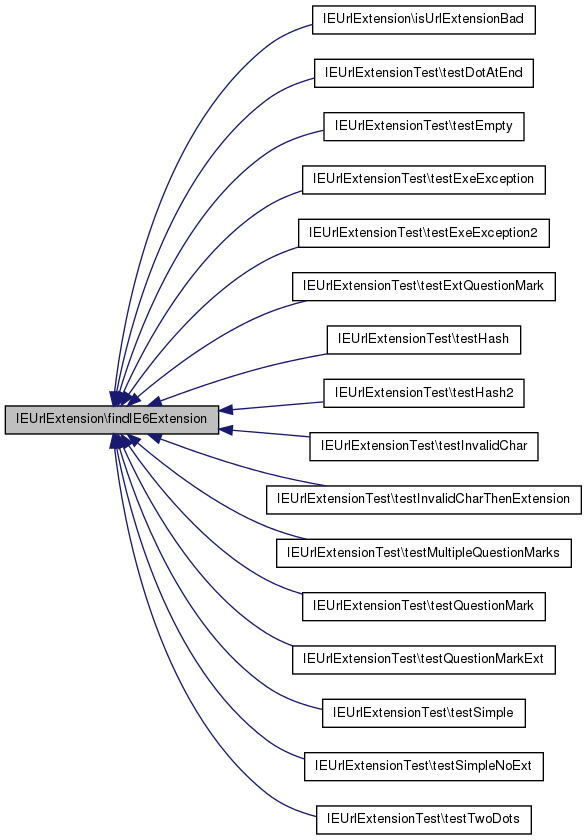
| static IEUrlExtension::findIE6Extension | ( | $ | url | ) | [static] |
Determine what extension IE6 will infer from a certain query string.
If the URL has an extension before the question mark, IE6 will use that and ignore the query string, but per the comment at isPathInfoBad() we don't have a reliable way to determine the URL, so isPathInfoBad() just passes in the query string for $url. All entry points have safe extensions (php, php5) anyway, so checking the query string is possibly overly paranoid but never insecure.
The criteria for finding an extension are as follows:
- a possible extension is a dot followed by one or more characters not in <>"/:|?.#
- if we find a possible extension followed by the end of the string or a #, that's our extension
- if we find a possible extension followed by a ?, that's our extension
- UNLESS it's exe, dll or cgi, in which case we ignore it and continue searching for another possible extension
- if we find a possible extension followed by a dot or another illegal character, we ignore it and continue searching
- Parameters:
-
$url string URL
- Returns:
- mixed Detected extension (string), or false if none found
Definition at line 173 of file IEUrlExtension.php.
References $url.
Referenced by isUrlExtensionBad(), IEUrlExtensionTest\testDotAtEnd(), IEUrlExtensionTest\testEmpty(), IEUrlExtensionTest\testExeException(), IEUrlExtensionTest\testExeException2(), IEUrlExtensionTest\testExtQuestionMark(), IEUrlExtensionTest\testHash(), IEUrlExtensionTest\testHash2(), IEUrlExtensionTest\testInvalidChar(), IEUrlExtensionTest\testInvalidCharThenExtension(), IEUrlExtensionTest\testMultipleQuestionMarks(), IEUrlExtensionTest\testQuestionMark(), IEUrlExtensionTest\testQuestionMarkExt(), IEUrlExtensionTest\testSimple(), IEUrlExtensionTest\testSimpleNoExt(), and IEUrlExtensionTest\testTwoDots().
| static IEUrlExtension::fixUrlForIE6 | ( | $ | url, |
| $ | extWhitelist = array() |
||
| ) | [static] |
Returns a variant of $url which will pass isUrlExtensionBad() but has the same GET parameters, or false if it can't figure one out.
- Parameters:
-
$url $extWhitelist array
- Returns:
- bool|string
Definition at line 121 of file IEUrlExtension.php.
References $url.
Referenced by WebRequest\checkUrlExtension().

| static IEUrlExtension::haveUndecodedRequestUri | ( | $ | serverSoftware | ) | [static] |
When passed the value of $_SERVER['SERVER_SOFTWARE'], this function returns true if that server is known to have a REQUEST_URI variable with %2E not decoded to ".".
On such a server, it is possible to detect whether the script filename has been obscured.
The function returns false if the server is not known to have this behaviour. Microsoft IIS in particular is known to decode escaped script filenames.
SERVER_SOFTWARE typically contains either a plain string such as "Zeus", or a specification in the style of a User-Agent header, such as "Apache/1.3.34 (Unix) mod_ssl/2.8.25 OpenSSL/0.9.8a PHP/4.4.2"
- Parameters:
-
$serverSoftware
- Returns:
- bool
Definition at line 239 of file IEUrlExtension.php.
| static IEUrlExtension::isUrlExtensionBad | ( | $ | urlPart, |
| $ | extWhitelist = array() |
||
| ) | [static] |
Given a right-hand portion of a URL, determine whether IE would detect a potentially harmful file extension.
- Parameters:
-
$urlPart string The right-hand portion of a URL $extWhitelist An array of file extensions which may occur in this URL, and which should be allowed.
- Returns:
- bool
Definition at line 80 of file IEUrlExtension.php.
References findIE6Extension().

The documentation for this class was generated from the following file:
- includes/libs/IEUrlExtension.php
