
Edition 2.0
1801 Varsity Drive
Raleigh, NC 27606-2072 USA
Phone: +1 919 754 3700
Phone: 888 733 4281
Fax: +1 919 754 3701
Mono-spaced Bold
To see the contents of the filemy_next_bestselling_novelin your current working directory, enter thecat my_next_bestselling_novelcommand at the shell prompt and press Enter to execute the command.
Press Enter to execute the command.Press Ctrl+Alt+F2 to switch to the first virtual terminal. Press Ctrl+Alt+F1 to return to your X-Windows session.
mono-spaced bold. For example:
File-related classes includefilesystemfor file systems,filefor files, anddirfor directories. Each class has its own associated set of permissions.
Choose → → from the main menu bar to launch Mouse Preferences. In the Buttons tab, click the Left-handed mouse check box and click to switch the primary mouse button from the left to the right (making the mouse suitable for use in the left hand).To insert a special character into a gedit file, choose → → from the main menu bar. Next, choose → from the Character Map menu bar, type the name of the character in the Search field and click . The character you sought will be highlighted in the Character Table. Double-click this highlighted character to place it in the Text to copy field and then click the button. Now switch back to your document and choose → from the gedit menu bar.
Mono-spaced Bold ItalicProportional Bold Italic
To connect to a remote machine using ssh, typesshat a shell prompt. If the remote machine isusername@domain.nameexample.comand your username on that machine is john, typessh [email protected].Themount -o remountcommand remounts the named file system. For example, to remount thefile-system/homefile system, the command ismount -o remount /home.To see the version of a currently installed package, use therpm -qcommand. It will return a result as follows:package.package-version-release
Publican is a DocBook publishing system.
mono-spaced roman and presented thus:
books Desktop documentation drafts mss photos stuff svn books_tests Desktop1 downloads images notes scripts svgs
mono-spaced roman but add syntax highlighting as follows:
package org.jboss.book.jca.ex1; import javax.naming.InitialContext; public class ExClient { public static void main(String args[]) throws Exception { InitialContext iniCtx = new InitialContext(); Object ref = iniCtx.lookup("EchoBean"); EchoHome home = (EchoHome) ref; Echo echo = home.create(); System.out.println("Created Echo"); System.out.println("Echo.echo('Hello') = " + echo.echo("Hello")); } }
6.
ls -l command to view file permissions:
$ ls -l file1 -rwxrw-r-- 1 user1 group1 0 2009-08-30 11:03 file1
rwx, control the access the Linux user1 user (in this case, the owner) has to file1. The next three permission bits, rw-, control the access the Linux group1 group has to file1. The last three permission bits, r--, control the access everyone else has to file1, which includes all users and processes.
ls -Z command:
$ ls -Z file1 -rwxrw-r-- user1 group1 unconfined_u:object_r:user_home_t:s0 file1
unconfined_u), a role (object_r), a type (user_home_t), and a level (s0). This information is used to make access control decisions. With DAC, access is controlled based only on Linux user and group IDs. It is important to remember that SELinux policy rules are checked after DAC rules. SELinux policy rules are not used if DAC rules deny access first.
sudo and su, as well as preventing them from executing files and applications in their home directory - if configured, this prevents users from executing malicious files from their home directories.
named daemon itself, and by other processes.
[1] "Integrating Flexible Support for Security Policies into the Linux Operating System", by Peter Loscocco and Stephen Smalley. This paper was originally prepared for the National Security Agency and is, consequently, in the public domain. Refer to the original paper for details and the document as it was first released. Any edits and changes were done by Murray McAllister.
[2] "Meeting Critical Security Objectives with Security-Enhanced Linux", by Peter Loscocco and Stephen Smalley. This paper was originally prepared for the National Security Agency and is, consequently, in the public domain. Refer to the original paper for details and the document as it was first released. Any edits and changes were done by Murray McAllister.
[3] Text files that include information, such as hostname to IP address mappings, that are used by DNS servers.
[4] Cox, Mark. "Risk report: Three years of Red Hat Enterprise Linux 4". Published 26 February 2008. Accessed 27 August 2009: http://www.redhatmagazine.com/2008/02/26/risk-report-three-years-of-red-hat-enterprise-linux-4/.
[5] Marti, Don. "A seatbelt for server software: SELinux blocks real-world exploits". Published 24 February 2008. Accessed 27 August 2009: http://www.linuxworld.com/news/2008/022408-selinux.html?page=1.
ls -Z command to view the SELinux context of files and directories:
$ ls -Z file1 -rwxrw-r-- user1 group1 unconfined_u:object_r:user_home_t:s0 file1
semanage login -l command as the Linux root user to view a list of mappings between SELinux and Linux user accounts:
# /usr/sbin/semanage login -l Login Name SELinux User MLS/MCS Range __default__ unconfined_u s0-s0:c0.c1023 root unconfined_u s0-s0:c0.c1023 system_u system_u s0-s0:c0.c1023
Login Name column lists Linux users, and the SELinux User column lists which SELinux user the Linux user is mapped to. For processes, the SELinux user limits which roles and levels are accessible. The last column, MLS/MCS Range, is the level used by Multi-Level Security (MLS) and Multi-Category Security (MCS). Levels are briefly discussed later.
s0-s0 is the same as s0). Each level is a sensitivity-category pair, with categories being optional. If there are categories, the level is written as sensitivity:category-set. If there are no categories, it is written as sensitivity.
c0.c3 is the same as c0,c1,c2,c3. The /etc/selinux/targeted/setrans.conf file maps levels (s0:c0) to human-readable form (ie. CompanyConfidential). Do not edit setrans.conf with a text editor: use semanage to make changes. Refer to the semanage(8) manual page for further information. In Red Hat Enterprise Linux, targeted policy enforces MCS, and in MCS, there is just one sensitivity, s0. MCS in Red Hat Enterprise Linux supports 1024 different categories: c0 through to c1023. s0-s0:c0.c1023 is sensitivity s0 and authorized for all categories.
entrypoint type for the new domain. The entrypoint permission is used in SELinux policy, and controls which applications can be used to enter a domain. The following example demonstrates a domain transition:
passwd application. The /usr/bin/passwd executable is labeled with the passwd_exec_t type:
$ ls -Z /usr/bin/passwd -rwsr-xr-x root root system_u:object_r:passwd_exec_t:s0 /usr/bin/passwd
/etc/shadow, which is labeled with the shadow_t type:
$ ls -Z /etc/shadow -r--------. root root system_u:object_r:shadow_t:s0 /etc/shadow
passwd_t domain are allowed to read and write to files labeled with the shadow_t type. The shadow_t type is only applied to files that are required for a password change. This includes /etc/gshadow, /etc/shadow, and their backup files.
passwd_t domain has entrypoint permission to the passwd_exec_t type.
/usr/bin/passwd application, the user's shell process transitions to the passwd_t domain. With SELinux, since the default action is to deny, and a rule exists that allows (among other things) applications running in the passwd_t domain to access files labeled with the shadow_t type, the passwd application is allowed to access /etc/shadow, and update the user's password.
passwd_t domain to access objects labeled with the shadow_t file type, other SELinux policy rules must be met before the subject can transition to a new domain. In this example, Type Enforcement ensures:
passwd_t domain can only be entered by executing an application labeled with the passwd_exec_t type; can only execute from authorized shared libraries, such as the lib_t type; and can not execute any other applications.
passwd_t, can write to files labeled with the shadow_t type. Even if other processes are running with superuser privileges, those processes can not write to files labeled with the shadow_t type, as they are not running in the passwd_t domain.
passwd_t domain. For example, the sendmail process running in the sendmail_t domain does not have a legitimate reason to execute passwd; therefore, it can never transition to the passwd_t domain.
passwd_t domain can only read and write to authorized types, such as files labeled with the etc_t or shadow_t types. This prevents the passwd application from being tricked into reading or writing arbitrary files.
ps -eZ command to view the SELinux context for processes. For example:
/usr/bin/passwd command. Do not enter a new password.
ps -eZ | grep passwd command. The output is similar to the following:
unconfined_u:unconfined_r:passwd_t:s0-s0:c0.c1023 13212 pts/1 00:00:00 passwd
Ctrl+C to cancel the passwd application.
/usr/bin/passwd application (labeled with the passwd_exec_t type) is executed, the user's shell process transitions to the passwd_t domain. Remember: the type defines a domain for processes, and a type for files.
ps -eZ command to view the SELinux contexts for running processes. The following is a truncated example of the output, and may differ on your system:
system_u:system_r:dhcpc_t:s0 1869 ? 00:00:00 dhclient system_u:system_r:sshd_t:s0-s0:c0.c1023 1882 ? 00:00:00 sshd system_u:system_r:gpm_t:s0 1964 ? 00:00:00 gpm system_u:system_r:crond_t:s0-s0:c0.c1023 1973 ? 00:00:00 crond system_u:system_r:kerneloops_t:s0 1983 ? 00:00:05 kerneloops system_u:system_r:crond_t:s0-s0:c0.c1023 1991 ? 00:00:00 atd
system_r role is used for system processes, such as daemons. Type Enforcement then separates each domain.
id -Z command to view the SELinux context associated with your Linux user:
unconfined_u:unconfined_r:unconfined_t:s0-s0:c0.c1023
unconfined_u user, running as the unconfined_r role, and is running in the unconfined_t domain. s0-s0 is an MLS range, which in this case, is the same as just s0. The categories the user has access to is defined by c0.c1023, which is all categories (c0 through to c1023).
unconfined_t domain, and system processes started by init run in the initrc_t domain - both of these domains are unconfined.
sshd or httpd, is confined in Red Hat Enterprise Linux. Also, most processes that run as the Linux root user and perform tasks for users, such as the passwd application, are confined. When a process is confined, it runs in its own domain, such as the httpd process running in the httpd_t domain. If a confined process is compromised by an attacker, depending on SELinux policy configuration, an attacker's access to resources and the possible damage they can do is limited.
httpd) from reading files that are not correctly labeled, such as files intended for use by Samba. This is an example, and should not be used in production. It assumes that the httpd and wget packages are installed, the SELinux targeted policy is used, and that SELinux is running in enforcing mode:
sestatus command to confirm that SELinux is enabled, is running in enforcing mode, and that targeted policy is being used:
$ /usr/sbin/sestatus SELinux status: enabled SELinuxfs mount: /selinux Current mode: enforcing Mode from config file: enforcing Policy version: 24 Policy from config file: targeted
SELinux status: enabled is returned when SELinux is enabled. Current mode: enforcing is returned when SELinux is running in enforcing mode. Policy from config file: targeted is returned when the SELinux targeted policy is used.
touch /var/www/html/testfile command to create a file.
ls -Z /var/www/html/testfile command to view the SELinux context:
-rw-r--r-- root root unconfined_u:object_r:httpd_sys_content_t:s0 /var/www/html/testfile
testfile file is labeled with the SELinux unconfined_u user. RBAC is used for processes, not files. Roles do not have a meaning for files - the object_r role is a generic role used for files (on persistent storage and network file systems). Under the /proc/ directory, files related to processes may use the system_r role.[6] The httpd_sys_content_t type allows the httpd process to access this file.
service httpd start command to start the httpd process. The output is as follows if httpd starts successfully:
# /sbin/service httpd start Starting httpd: [ OK ]
wget http://localhost/testfile command. Unless there are changes to the default configuration, this command succeeds:
--2009-11-06 17:43:01-- http://localhost/testfile Resolving localhost... 127.0.0.1 Connecting to localhost|127.0.0.1|:80... connected. HTTP request sent, awaiting response... 200 OK Length: 0 [text/plain] Saving to: `testfile' [ <=> ] 0 --.-K/s in 0s 2009-11-06 17:43:01 (0.00 B/s) - `testfile' saved [0/0]
chcon command relabels files; however, such label changes do not survive when the file system is relabeled. For permanent changes that survive a file system relabel, use the semanage command, which is discussed later. As the Linux root user, run the following command to change the type to a type used by Samba:
chcon -t samba_share_t /var/www/html/testfile
ls -Z /var/www/html/testfile command to view the changes:
-rw-r--r-- root root unconfined_u:object_r:samba_share_t:s0 /var/www/html/testfile
httpd process access to testfile. Change into a directory where your Linux user has write access to, and run the wget http://localhost/testfile command. Unless there are changes to the default configuration, this command fails:
--2009-11-06 14:11:23-- http://localhost/testfile Resolving localhost... 127.0.0.1 Connecting to localhost|127.0.0.1|:80... connected. HTTP request sent, awaiting response... 403 Forbidden 2009-11-06 14:11:23 ERROR 403: Forbidden.
rm -i /var/www/html/testfile command to remove testfile.
httpd to be running, as the Linux root user, run the service httpd stop command to stop httpd:
# /sbin/service httpd stop Stopping httpd: [ OK ]
httpd process access to testfile in step 7, because the file was labeled with a type that the httpd process does not have access to, SELinux denied access.
/var/log/audit/audit.log:
type=AVC msg=audit(1220706212.937:70): avc: denied { getattr } for pid=1904 comm="httpd" path="/var/www/html/testfile" dev=sda5 ino=247576 scontext=unconfined_u:system_r:httpd_t:s0 tcontext=unconfined_u:object_r:samba_share_t:s0 tclass=file
type=SYSCALL msg=audit(1220706212.937:70): arch=40000003 syscall=196 success=no exit=-13 a0=b9e21da0 a1=bf9581dc a2=555ff4 a3=2008171 items=0 ppid=1902 pid=1904 auid=500 uid=48 gid=48 euid=48 suid=48 fsuid=48 egid=48 sgid=48 fsgid=48 tty=(none) ses=1 comm="httpd" exe="/usr/sbin/httpd" subj=unconfined_u:system_r:httpd_t:s0 key=(null)
/var/log/httpd/error_log:
[Wed May 06 23:00:54 2009] [error] [client 127.0.0.1] (13)Permission denied: access to /testfile denied
initrc_t domain, unconfined kernel processes run in the kernel_t domain, and unconfined Linux users run in the unconfined_t domain. For unconfined processes, SELinux policy rules are applied, but policy rules exist that allow processes running in unconfined domains almost all access. Processes running in unconfined domains fall back to using DAC rules exclusively. If an unconfined process is compromised, SELinux does not prevent an attacker from gaining access to system resources and data, but of course, DAC rules are still used. SELinux is a security enhancement on top of DAC rules - it does not replace them.
httpd) can access data intended for use by Samba, when running unconfined. Note: in Red Hat Enterprise Linux, the httpd process runs in the confined httpd_t domain by default. This is an example, and should not be used in production. It assumes that the httpd, wget, dbus and audit packages are installed, that the SELinux targeted policy is used, and that SELinux is running in enforcing mode:
sestatus command to confirm that SELinux is enabled, is running in enforcing mode, and that targeted policy is being used:
$ /usr/sbin/sestatus SELinux status: enabled SELinuxfs mount: /selinux Current mode: enforcing Mode from config file: enforcing Policy version: 24 Policy from config file: targeted
SELinux status: enabled is returned when SELinux is enabled. Current mode: enforcing is returned when SELinux is running in enforcing mode. Policy from config file: targeted is returned when the SELinux targeted policy is used.
touch /var/www/html/test2file command to create a file.
ls -Z /var/www/html/test2file command to view the SELinux context:
-rw-r--r-- root root unconfined_u:object_r:httpd_sys_content_t:s0 /var/www/html/test2file
test2file file is labeled with the SELinux unconfined_u user. RBAC is used for processes, not files. Roles do not have a meaning for files - the object_r role is a generic role used for files (on persistent storage and network file systems). Under the /proc/ directory, files related to processes may use the system_r role.[7] The httpd_sys_content_t type allows the httpd process to access this file.
chcon command relabels files; however, such label changes do not survive when the file system is relabeled. For permanent changes that survive a file system relabel, use the semanage command, which is discussed later. As the Linux root user, run the following command to change the type to a type used by Samba:
chcon -t samba_share_t /var/www/html/test2file
ls -Z /var/www/html/test2file command to view the changes:
-rw-r--r-- root root unconfined_u:object_r:samba_share_t:s0 /var/www/html/test2file
service httpd status command to confirm that the httpd process is not running:
$ /sbin/service httpd status httpd is stopped
service httpd stop command as the Linux root user to stop the httpd process:
# /sbin/service httpd stop Stopping httpd: [ OK ]
httpd process run unconfined, run the following command as the Linux root user to change the type of /usr/sbin/httpd, to a type that does not transition to a confined domain:
chcon -t unconfined_exec_t /usr/sbin/httpd
ls -Z /usr/sbin/httpd command to confirm that /usr/sbin/httpd is labeled with the unconfined_exec_t type:
-rwxr-xr-x root root system_u:object_r:unconfined_exec_t /usr/sbin/httpd
service httpd start command to start the httpd process. The output is as follows if httpd starts successfully:
# /sbin/service httpd start Starting httpd: [ OK ]
ps -eZ | grep httpd command to view the httpd running in the unconfined_t domain:
$ ps -eZ | grep httpd unconfined_u:system_r:unconfined_t7721? 00:00:00 httpd unconfined_u:system_r:unconfined_t7723? 00:00:00 httpd unconfined_u:system_r:unconfined_t7724? 00:00:00 httpd unconfined_u:system_r:unconfined_t7725? 00:00:00 httpd unconfined_u:system_r:unconfined_t7726? 00:00:00 httpd unconfined_u:system_r:unconfined_t7727? 00:00:00 httpd unconfined_u:system_r:unconfined_t7728? 00:00:00 httpd unconfined_u:system_r:unconfined_t7729? 00:00:00 httpd unconfined_u:system_r:unconfined_t7730? 00:00:00 httpd
wget http://localhost/test2file command. Unless there are changes to the default configuration, this command succeeds:
--2009-05-07 01:41:10-- http://localhost/test2file Resolving localhost... 127.0.0.1 Connecting to localhost|127.0.0.1|:80... connected. HTTP request sent, awaiting response... 200 OK Length: 0 [text/plain] Saving to: `test2file.1' [ <=> ]--.-K/s in 0s 2009-05-07 01:41:10 (0.00 B/s) - `test2file.1' saved [0/0]
httpd process does not have access to files labeled with the samba_share_t type, httpd is running in the unconfined unconfined_t domain, and falls back to using DAC rules, and as such, the wget command succeeds. Had httpd been running in the confined httpd_t domain, the wget command would have failed.
restorecon command restores the default SELinux context for files. As the Linux root user, run the restorecon -v /usr/sbin/httpd command to restore the default SELinux context for /usr/sbin/httpd:
# /sbin/restorecon -v /usr/sbin/httpd restorecon reset /usr/sbin/httpd context system_u:object_r:unconfined_notrans_exec_t:s0->system_u:object_r:httpd_exec_t:s0
ls -Z /usr/sbin/httpd command to confirm that /usr/sbin/httpd is labeled with the httpd_exec_t type:
$ ls -Z /usr/sbin/httpd -rwxr-xr-x root root system_u:object_r:httpd_exec_t /usr/sbin/httpd
/sbin/service httpd restart command to restart httpd. After restarting, run the ps -eZ | grep httpd to confirm that httpd is running in the confined httpd_t domain:
# /sbin/service httpd restart Stopping httpd: [ OK ] Starting httpd: [ OK ] # ps -eZ | grep httpd unconfined_u:system_r:httpd_t 8880 ? 00:00:00 httpd unconfined_u:system_r:httpd_t 8882 ? 00:00:00 httpd unconfined_u:system_r:httpd_t 8883 ? 00:00:00 httpd unconfined_u:system_r:httpd_t 8884 ? 00:00:00 httpd unconfined_u:system_r:httpd_t 8885 ? 00:00:00 httpd unconfined_u:system_r:httpd_t 8886 ? 00:00:00 httpd unconfined_u:system_r:httpd_t 8887 ? 00:00:00 httpd unconfined_u:system_r:httpd_t 8888 ? 00:00:00 httpd unconfined_u:system_r:httpd_t 8889 ? 00:00:00 httpd
rm -i /var/www/html/test2file command to remove test2file.
httpd to be running, as the Linux root user, run the service httpd stop command to stop httpd:
# /sbin/service httpd stop Stopping httpd: [ OK ]
semanage login -l command as the Linux root user:
# /usr/sbin/semanage login -l Login Name SELinux User MLS/MCS Range __default__ unconfined_u s0-s0:c0.c1023 root unconfined_u s0-s0:c0.c1023 system_u system_u s0-s0:c0.c1023
__default__ login by default (which is mapped to the SELinux unconfined_u user). The following defines the default-mapping:
__default__ unconfined_u s0-s0:c0.c1023
unconfined_u user. It assumes that the Linux root user is running unconfined, as it does by default in Red Hat Enterprise Linux 6:
/usr/sbin/useradd newuser command to create a new Linux user named newuser.
passwd newuser command to assign a password to the Linux newuser user:
# passwd newuser Changing password for user newuser. New UNIX password:Enter a passwordRetype new UNIX password:Enter the same password againpasswd: all authentication tokens updated successfully.
id -Z command to view the context of a Linux user:
[newuser@localhost ~]$ id -Z unconfined_u:unconfined_r:unconfined_t:s0-s0:c0.c1023
/usr/sbin/userdel -r newuser command as the Linux root user to remove it, along with the Linux newuser's home directory.
unconfined_t domain to its own confined domain, unconfined Linux users are still subject to the restrictions of that confined domain. The security benefit of this is that, even though a Linux user is running unconfined, the application remains confined, and therefore, the exploitation of a flaw in the application can be limited by policy. Note: this does not protect the system from the user. Instead, the user and the system are being protected from possible damage caused by a flaw in the application.
| User | Domain | X Window System | su and sudo | Execute in home directory and /tmp/ | Networking |
|---|---|---|---|---|---|
| guest_u | guest_t | no | no | optional | no |
| xguest_u | xguest_t | yes | no | optional | only Firefox |
| user_u | user_t | yes | no | optional | yes |
| staff_u | staff_t | yes |
only sudo
| optional | yes |
guest_t, xguest_t, and user_t domains can only run set user ID (setuid) applications if SELinux policy permits it (such as passwd). They can not run the su and /usr/bin/sudo setuid applications, and therefore, can not use these applications to become the Linux root user.
guest_t domain have no network access, and can only log in via a terminal (including ssh; they can log in via ssh, but can not use ssh to connect to another system).
xguest_t domain have is Firefox connecting to web pages.
xguest_t, user_t and staff_t domains can log in via the X Window System and a terminal.
staff_t domain do not have permissions to execute applications with /usr/bin/sudo. These permissions must be configured by an administrator.
guest_t and xguest_t domains can not execute applications in their home directories or /tmp/, preventing them from executing applications (which inherit users' permissions) in directories they have write access to. This helps prevent flawed or malicious applications from modifying files users' own.
user_t and staff_t domains can execute applications in their home directories and /tmp/. Refer to Section 6.6, “Booleans for Users Executing Applications” for information about allowing and preventing users from executing applications in their home directories and /tmp/.
mount command; mounting NFS file systems; and how to preserve SELinux contexts when copying and archiving files and directories.
semanage, audit2allow, audit2why and chcat, for operating and managing SELinux.
restorecon, secon, setfiles, semodule, load_policy, and setsebool, for operating and managing SELinux.
system-config-selinux, a graphical tool for managing SELinux.
/usr/share/selinux/devel/policygentool and /usr/share/selinux/devel/policyhelp, as well as example policy files.
policy: provides SELinux policies. For targeted policy, install selinux-policy-targeted. For MLS, install selinux-policy-mls.
sealert (which is provided by this package).
apol, seaudit, and sediffx tools. The setools-console package provides the seaudit-report, sechecker, sediff, seinfo, sesearch, findcon, replcon, and indexcon command line tools. Refer to the Tresys Technology SETools page for information about these tools.
avcstat, getenforce, getsebool, matchpathcon, selinuxconlist, selinuxdefcon, selinuxenabled, setenforce, togglesebool tools.
s0-s0:c0.c1023, to an easier to read form, such as SystemLow-SystemHigh. This package is not installed by default.
yum install package-name command. For example, to install the mcstrans package, run the yum install mcstrans command. To upgrade all installed packages in Red Hat Enterprise Linux, run the yum update command.
/var/log/audit/audit.log by default:
type=AVC msg=audit(1223024155.684:49): avc: denied { getattr } for pid=2000 comm="httpd" path="/var/www/html/file1" dev=dm-0 ino=399185 scontext=unconfined_u:system_r:httpd_t:s0 tcontext=system_u:object_r:samba_share_t:s0 tclass=file
May 7 18:55:56 localhost setroubleshoot: SELinux is preventing httpd (httpd_t) "getattr" to /var/www/html/file1 (samba_share_t). For complete SELinux messages. run sealert -l de7e30d6-5488-466d-a606-92c9f40d316d
setroubleshootd no longer constantly runs as a service, however it is still used to analyze the AVC messages. Two new programs act as a method to start setroubleshoot when needed: sedispatch and seapplet. sedispatch runs as part of the audit subsystem, and via dbus, sends a message when an AVC denial occurs, which will go straight to setroubleshootd if it is already running, or it will start setroubleshootd if it is not running. seapplet is a tool which runs in the system's toolbar, waiting for dbus messages in setroubleshootd, and will launch the notification bubble, allowing the user to review the denial.
auditd and rsyslogd daemons to automatically start at boot, run the following commands as the Linux root user:
/sbin/chkconfig --levels 2345 auditd on
/sbin/chkconfig --levels 2345 rsyslog on
service service-name status command to check if these services are running, for example:
$ /sbin/service auditd status
auditd (pid 1318) is running...
service-name is stoppedservice service-name start command as the Linux root user to start them. For example:
# /sbin/service auditd start Starting auditd: [ OK ]
/etc/selinux/config file is the main SELinux configuration file. It controls the SELinux mode and the SELinux policy to use:
# This file controls the state of SELinux on the system. # SELINUX= can take one of these three values: # enforcing - SELinux security policy is enforced. # permissive - SELinux prints warnings instead of enforcing. # disabled - No SELinux policy is loaded. SELINUX=enforcing # SELINUXTYPE= can take one of these two values: # targeted - Targeted processes are protected, # mls - Multi Level Security protection. SELINUXTYPE=targeted
SELINUX=enforcingSELINUX option sets the mode SELinux runs in. SELinux has three modes: enforcing, permissive, and disabled. When using enforcing mode, SELinux policy is enforced, and SELinux denies access based on SELinux policy rules. Denial messages are logged. When using permissive mode, SELinux policy is not enforced. SELinux does not deny access, but denials are logged for actions that would have been denied if running SELinux in enforcing mode. When using disabled mode, SELinux is disabled (the SELinux module is not registered with the Linux kernel), and only DAC rules are used.
SELINUXTYPE=targetedSELINUXTYPE option sets the SELinux policy to use. Targeted policy is the default policy. Only change this option if you want to use the MLS policy. To use the MLS policy, install the selinux-policy-mls package; configure SELINUXTYPE=mls in /etc/selinux/config; and reboot your system.
/usr/sbin/getenforce or /usr/sbin/sestatus commands to check the status of SELinux. The getenforce command returns Enforcing, Permissive, or Disabled. The getenforce command returns Enforcing when SELinux is enabled (SELinux policy rules are enforced):
$ /usr/sbin/getenforce Enforcing
getenforce command returns Permissive when SELinux is enabled, but SELinux policy rules are not enforced, and only DAC rules are used. The getenforce command returns Disabled if SELinux is disabled.
sestatus command returns the SELinux status and the SELinux policy being used:
$ /usr/sbin/sestatus SELinux status: enabled SELinuxfs mount: /selinux Current mode: enforcing Mode from config file: enforcing Policy version: 23 Policy from config file: targeted
SELinux status: enabled is returned when SELinux is enabled. Current mode: enforcing is returned when SELinux is running in enforcing mode. Policy from config file: targeted is returned when the SELinux targeted policy is used.
SELINUX=disabled option is configured in /etc/selinux/config:
# This file controls the state of SELinux on the system. # SELINUX= can take one of these three values: # enforcing - SELinux security policy is enforced. # permissive - SELinux prints warnings instead of enforcing. # disabled - No SELinux policy is loaded. SELINUX=disabled # SELINUXTYPE= can take one of these two values: # targeted - Targeted processes are protected, # mls - Multi Level Security protection. SELINUXTYPE=targeted
getenforce command returns Disabled:
$ /usr/sbin/getenforce Disabled
rpm -qa | grep selinux, rpm -q policycoreutils, and rpm -qa | grep setroubleshoot commands to confirm that the SELinux packages are installed. This guide assumes the following packages are installed: selinux-policy-targeted, selinux-policy, libselinux, libselinux-python, libselinux-utils, policycoreutils, policycoreutils-python, setroubleshoot, setroubleshoot-server, setroubleshoot-plugins. If these packages are not installed, as the Linux root user, install them via the yum install package-name command. The following packages are optional: policycoreutils-gui, setroubleshoot, selinux-policy-devel, and mcstrans.
SELINUX=permissive in /etc/selinux/config:
# This file controls the state of SELinux on the system. # SELINUX= can take one of these three values: # enforcing - SELinux security policy is enforced. # permissive - SELinux prints warnings instead of enforcing. # disabled - No SELinux policy is loaded. SELINUX=permissive # SELINUXTYPE= can take one of these two values: # targeted - Targeted processes are protected, # mls - Multi Level Security protection. SELINUXTYPE=targeted
reboot command to restart the system. During the next boot, file systems are labeled. The label process labels all files with an SELinux context:
*** Warning -- SELinux targeted policy relabel is required. *** Relabeling could take a very long time, depending on file *** system size and speed of hard drives. ****
* character on the bottom line represents 1000 files that have been labeled. In the above example, four * characters represent 4000 files have been labeled. The time it takes to label all files depends upon the number of files on the system, and the speed of the hard disk drives. On modern systems, this process can take as little as 10 minutes.
grep "SELinux is preventing" /var/log/messages command as the Linux root user to confirm that SELinux did not deny actions during the last boot. If SELinux did not deny actions during the last boot, this command does not return any output. Refer to Chapter 8, Troubleshooting for troubleshooting information if SELinux denied access during boot.
/var/log/messages, configure SELINUX=enforcing in /etc/selinux/config:
# This file controls the state of SELinux on the system. # SELINUX= can take one of these three values: # enforcing - SELinux security policy is enforced. # permissive - SELinux prints warnings instead of enforcing. # disabled - No SELinux policy is loaded. SELINUX=enforcing # SELINUXTYPE= can take one of these two values: # targeted - Targeted processes are protected, # mls - Multi Level Security protection. SELINUXTYPE=targeted
getenforce command returns Enforcing:
$ /usr/sbin/getenforce Enforcing
/usr/sbin/semanage login -l command to view the mapping between SELinux and Linux users. The output should be as follows:
Login Name SELinux User MLS/MCS Range __default__ unconfined_u s0-s0:c0.c1023 root unconfined_u s0-s0:c0.c1023 system_u system_u s0-s0:c0.c1023
SELinux-user username is already defined warnings if they occur, where username can be unconfined_u, guest_u, or xguest_u:
/usr/sbin/semanage user -a -S targeted -P user -R "unconfined_r system_r" -r s0-s0:c0.c1023 unconfined_u
/usr/sbin/semanage login -m -S targeted -s "unconfined_u" -r s0-s0:c0.c1023 __default__
/usr/sbin/semanage login -m -S targeted -s "unconfined_u" -r s0-s0:c0.c1023 root
/usr/sbin/semanage user -a -S targeted -P user -R guest_r guest_u
/usr/sbin/semanage user -a -S targeted -P user -R xguest_r xguest_u
SELINUX=disabled in /etc/selinux/config:
# This file controls the state of SELinux on the system. # SELINUX= can take one of these three values: # enforcing - SELinux security policy is enforced. # permissive - SELinux prints warnings instead of enforcing. # disabled - No SELinux policy is loaded. SELINUX=disabled # SELINUXTYPE= can take one of these two values: # targeted - Targeted processes are protected, # mls - Multi Level Security protection. SELINUXTYPE=targeted
getenforce command returns Disabled:
$ /usr/sbin/getenforce Disabled
/usr/sbin/setenforce command to change between enforcing and permissive mode. Changes made with /usr/sbin/setenforce do not persist across reboots. To change to enforcing mode, as the Linux root user, run the /usr/sbin/setenforce 1 command. To change to permissive mode, run the /usr/sbin/setenforce 0 command. Use the /usr/sbin/getenforce command to view the current SELinux mode.
semanage boolean -l command as the Linux root user. The following example does not list all Booleans:
# /usr/sbin/semanage boolean -l SELinux boolean Description ftp_home_dir -> off Allow ftp to read and write files in the user home directories xen_use_nfs -> off Allow xen to manage nfs files xguest_connect_network -> on Allow xguest to configure Network Manager
SELinux boolean column lists Boolean names. The Description column lists whether the Booleans are on or off, and what they do.
ftp_home_dir Boolean is off, preventing the FTP daemon (vsftpd) from reading and writing to files in user home directories:
ftp_home_dir -> off Allow ftp to read and write files in the user home directories
getsebool -a command lists Booleans, whether they are on or off, but does not give a description of each one. The following example does not list all Booleans:
$ /usr/sbin/getsebool -a allow_console_login --> off allow_cvs_read_shadow --> off allow_daemons_dump_core --> on
getsebool boolean-name command to only list the status of the boolean-name Boolean:
$ /usr/sbin/getsebool allow_console_login allow_console_login --> off
$ /usr/sbin/getsebool allow_console_login allow_cvs_read_shadow allow_daemons_dump_core allow_console_login --> off allow_cvs_read_shadow --> off allow_daemons_dump_core --> on
setsebool boolean-name x command turns Booleans on or off, where boolean-name is a Boolean name, and x is either on to turn the Boolean on, or off to turn it off.
httpd_can_network_connect_db Boolean:
httpd_can_network_connect_db Boolean is off, preventing Apache HTTP Server scripts and modules from connecting to database servers:
$ /usr/sbin/getsebool httpd_can_network_connect_db httpd_can_network_connect_db --> off
setsebool httpd_can_network_connect_db on command as the Linux root user.
getsebool httpd_can_network_connect_db command to verify the Boolean is turned on:
$ /usr/sbin/getsebool httpd_can_network_connect_db httpd_can_network_connect_db --> on
setsebool -P boolean-name on command as the Linux root user:
# /usr/sbin/setsebool -P httpd_can_network_connect_db on
setsebool httpd_can_network_connect_db off command. For changes that persist across reboots, run the setsebool -P httpd_can_network_connect_db off command.
nfs_t type. Also, by default, Samba shares mounted on the client side are labeled with a default context defined by policy. In common policies, this default context uses the cifs_t type.
nfs_t or cifs_t types. This may prevent file systems labeled with these types from being mounted and then read or exported by other services. Booleans can be turned on or off to control which services are allowed to access the nfs_t and cifs_t types.
setsebool and semanage commands must be run as the Linux root user. The setsebool -P command makes persistent changes. Do not use the -P option if you do not want changes to persist across reboots:
nfs_t type):
/usr/sbin/setsebool -P httpd_use_nfs on
cifs_t type):
/usr/sbin/setsebool -P httpd_use_cifs on
/usr/sbin/setsebool -P samba_share_nfs on
vsftpd)/usr/sbin/setsebool -P allow_ftpd_use_nfs on
/usr/sbin/setsebool -P allow_ftpd_use_cifs on
/usr/sbin/semanage boolean -l | grep nfs
/usr/sbin/semanage boolean -l | grep cifs
ls -Z command:
$ ls -Z file1 -rw-rw-r-- user1 group1 unconfined_u:object_r:user_home_t:s0 file1
unconfined_u), a role (object_r), a type (user_home_t), and a level (s0). This information is used to make access control decisions. On DAC systems, access is controlled based on Linux user and group IDs. SELinux policy rules are checked after DAC rules. SELinux policy rules are not used if DAC rules deny access first.
chcon, semanage fcontext, and restorecon.
chcon command changes the SELinux context for files. However, changes made with the chcon command do not survive a file system relabel, or the execution of the /sbin/restorecon command. SELinux policy controls whether users are able to modify the SELinux context for any given file. When using chcon, users provide all or part of the SELinux context to change. An incorrect file type is a common cause of SELinux denying access.
chcon -t type file-name command to change the file type, where type is a type, such as httpd_sys_content_t, and file-name is a file or directory name.
chcon -R -t type directory-name command to change the type of the directory and its contents, where type is a type, such as httpd_sys_content_t, and directory-name is a directory name.
cd command without arguments to change into your home directory.
touch file1 command to create a new file. Use the ls -Z file1 command to view the SELinux context for file1:
$ ls -Z file1 -rw-rw-r-- user1 group1 unconfined_u:object_r:user_home_t:s0 file1
file1 includes the SELinux unconfined_u user, object_r role, user_home_t type, and the s0 level. For a description of each part of the SELinux context, refer to Chapter 3, SELinux Contexts.
chcon -t samba_share_t file1 command to change the type to samba_share_t. The -t option only changes the type. View the change with ls -Z file1:
$ ls -Z file1 -rw-rw-r-- user1 group1 unconfined_u:object_r:samba_share_t:s0 file1
/sbin/restorecon -v file1 command to restore the SELinux context for the file1 file. Use the -v option to view what changes:
$ /sbin/restorecon -v file1 restorecon reset file1 context unconfined_u:object_r:samba_share_t:s0->system_u:object_r:user_home_t:s0
samba_share_t, is restored to the correct, user_home_t type. When using targeted policy (the default SELinux policy in Red Hat Enterprise Linux 6), the /sbin/restorecon command reads the files in the /etc/selinux/targeted/contexts/files/ directory, to see which SELinux context files should have.
file1 was a directory.
/var/www/html/):
mkdir /web command to create a new directory, and then the touch /web/file{1,2,3} command to create 3 empty files (file1, file2, and file3). The /web/ directory and files in it are labeled with the default_t type:
# ls -dZ /web drwxr-xr-x root root unconfined_u:object_r:default_t:s0 /web # ls -lZ /web -rw-r--r-- root root unconfined_u:object_r:default_t:s0 file1 -rw-r--r-- root root unconfined_u:object_r:default_t:s0 file2 -rw-r--r-- root root unconfined_u:object_r:default_t:s0 file3
chcon -R -t httpd_sys_content_t /web/ command to change the type of the /web/ directory (and its contents) to httpd_sys_content_t:
# chcon -R -t httpd_sys_content_t /web/ # ls -dZ /web/ drwxr-xr-x root root unconfined_u:object_r:httpd_sys_content_t:s0 /web/ # ls -lZ /web/ -rw-r--r-- root root unconfined_u:object_r:httpd_sys_content_t:s0 file1 -rw-r--r-- root root unconfined_u:object_r:httpd_sys_content_t:s0 file2 -rw-r--r-- root root unconfined_u:object_r:httpd_sys_content_t:s0 file3
/sbin/restorecon -R -v /web/ command to restore the default SELinux contexts:
# /sbin/restorecon -R -v /web/ restorecon reset /web context unconfined_u:object_r:httpd_sys_content_t:s0->system_u:object_r:default_t:s0 restorecon reset /web/file2 context unconfined_u:object_r:httpd_sys_content_t:s0->system_u:object_r:default_t:s0 restorecon reset /web/file3 context unconfined_u:object_r:httpd_sys_content_t:s0->system_u:object_r:default_t:s0 restorecon reset /web/file1 context unconfined_u:object_r:httpd_sys_content_t:s0->system_u:object_r:default_t:s0
chcon.
/usr/sbin/semanage fcontext command changes the SELinux context for files. When using targeted policy, changes made with this command are added to the /etc/selinux/targeted/contexts/files/file_contexts file if the changes are to files that exists in file_contexts, or are added to file_contexts.local for new files and directories, such as creating a /web/ directory. setfiles, which is used when a file system is relabeled, and /sbin/restorecon, which restores the default SELinux contexts, read these files. This means that changes made by /usr/sbin/semanage fcontext are persistent, even if the file system is relabeled. SELinux policy controls whether users are able to modify the SELinux context for any given file.
/usr/sbin/semanage fcontext -a options file-name|directory-name command, remembering to use the full path to the file or directory.
/sbin/restorecon -v file-name|directory-name command to apply the context changes.
touch /etc/file1 command to create a new file. By default, newly-created files in the /etc/ directory are labeled with the etc_t type:
# ls -Z /etc/file1 -rw-r--r-- root root unconfined_u:object_r:etc_t:s0 /etc/file1
/usr/sbin/semanage fcontext -a -t samba_share_t /etc/file1 command to change the file1 type to samba_share_t. The -a option adds a new record, and the -t option defines a type (samba_share_t). Note: running this command does not directly change the type - file1 is still labeled with the etc_t type:
# /usr/sbin/semanage fcontext -a -t samba_share_t /etc/file1 # ls -Z /etc/file1 -rw-r--r-- root root unconfined_u:object_r:etc_t:s0 /etc/file1
/usr/sbin/semanage fcontext -a -t samba_share_t /etc/file1 command adds the following entry to /etc/selinux/targeted/contexts/files/file_contexts.local:
/etc/file1 unconfined_u:object_r:samba_share_t:s0
/sbin/restorecon -v /etc/file1 command to change the type. Since the semanage command added an entry to file.contexts.local for /etc/file1, the /sbin/restorecon command changes the type to samba_share_t:
# /sbin/restorecon -v /etc/file1 restorecon reset /etc/file1 context unconfined_u:object_r:etc_t:s0->system_u:object_r:samba_share_t:s0
rm -i /etc/file1 command to remove file1.
/usr/sbin/semanage fcontext -d /etc/file1 command to remove the context added for /etc/file1. When the context is removed, running restorecon changes the type to etc_t, rather than samba_share_t.
mkdir /web command to create a new directory. This directory is labeled with the default_t type:
# ls -dZ /web drwxr-xr-x root root unconfined_u:object_r:default_t:s0 /web
ls -d option makes ls list information about a directory, rather than its contents, and the -Z option makes ls display the SELinux context (in this example, unconfined_u:object_r:default_t:s0).
/usr/sbin/semanage fcontext -a -t httpd_sys_content_t /web command to change the /web/ type to httpd_sys_content_t. The -a option adds a new record, and the -t option defines a type (httpd_sys_content_t). Note: running this command does not directly change the type - /web/ is still labeled with the default_t type:
# /usr/sbin/semanage fcontext -a -t httpd_sys_content_t /web # ls -dZ /web drwxr-xr-x root root unconfined_u:object_r:default_t:s0 /web
/usr/sbin/semanage fcontext -a -t httpd_sys_content_t /web command adds the following entry to /etc/selinux/targeted/contexts/files/file_contexts.local:
/web unconfined_u:object_r:httpd_sys_content_t:s0
/sbin/restorecon -v /web command to change the type. Since the semanage command added an entry to file.contexts.local for /web, the /sbin/restorecon command changes the type to httpd_sys_content_t:
# /sbin/restorecon -v /web restorecon reset /web context unconfined_u:object_r:default_t:s0->system_u:object_r:httpd_sys_content_t:s0
/web/, files and directories created in the /web/ directory are labeled with the httpd_sys_content_t type.
/usr/sbin/semanage fcontext -d /web command to remove the context added for /web/.
/sbin/restorecon -v /web command to restore the default SELinux context.
/var/www/html/):
mkdir /web command to create a new directory, and then the touch /web/file{1,2,3} command to create 3 empty files (file1, file2, and file3). The /web/ directory and files in it are labeled with the default_t type:
# ls -dZ /web drwxr-xr-x root root unconfined_u:object_r:default_t:s0 /web # ls -lZ /web -rw-r--r-- root root unconfined_u:object_r:default_t:s0 file1 -rw-r--r-- root root unconfined_u:object_r:default_t:s0 file2 -rw-r--r-- root root unconfined_u:object_r:default_t:s0 file3
/usr/sbin/semanage fcontext -a -t httpd_sys_content_t "/web(/.*)?" command to change the type of the /web/ directory and the files in it, to httpd_sys_content_t. The -a option adds a new record, and the -t option defines a type (httpd_sys_content_t). The "/web(/.*)?" regular expression causes the semanage command to apply changes to the /web/ directory, as well as the files in it. Note: running this command does not directly change the type - /web/ and files in it are still labeled with the default_t type:
# ls -dZ /web drwxr-xr-x root root unconfined_u:object_r:default_t:s0 /web # ls -lZ /web -rw-r--r-- root root unconfined_u:object_r:default_t:s0 file1 -rw-r--r-- root root unconfined_u:object_r:default_t:s0 file2 -rw-r--r-- root root unconfined_u:object_r:default_t:s0 file3
/usr/sbin/semanage fcontext -a -t httpd_sys_content_t "/web(/.*)?" command adds the following entry to /etc/selinux/targeted/contexts/files/file_contexts.local:
/web(/.*)? system_u:object_r:httpd_sys_content_t:s0
/sbin/restorecon -R -v /web command to change the type of the /web/ directory, as well as all files in it. The -R is for recursive, which means all files and directories under the /web/ directory are labeled with the httpd_sys_content_t type. Since the semanage command added an entry to file.contexts.local for /web(/.*)?, the /sbin/restorecon command changes the types to httpd_sys_content_t:
# /sbin/restorecon -R -v /web restorecon reset /web context unconfined_u:object_r:default_t:s0->system_u:object_r:httpd_sys_content_t:s0 restorecon reset /web/file2 context unconfined_u:object_r:default_t:s0->system_u:object_r:httpd_sys_content_t:s0 restorecon reset /web/file3 context unconfined_u:object_r:default_t:s0->system_u:object_r:httpd_sys_content_t:s0 restorecon reset /web/file1 context unconfined_u:object_r:default_t:s0->system_u:object_r:httpd_sys_content_t:s0
/web/ directory will be labeled with the httpd_sys_content_t type.
/usr/sbin/semanage fcontext -d "/web(/.*)?" command to remove the context added for "/web(/.*)?".
/sbin/restorecon -R -v /web command to restore the default SELinux contexts.
/usr/sbin/semanage fcontext -a -t httpd_sys_content_t /test command. The /test/ directory does not have to exist. This command adds the following context to /etc/selinux/targeted/contexts/files/file_contexts.local:
/test system_u:object_r:httpd_sys_content_t:s0
/usr/sbin/semanage fcontext -d file-name|directory-name command, where file-name|directory-name is the first part in file_contexts.local. The following is an example of a context in file_contexts.local:
/test system_u:object_r:httpd_sys_content_t:s0
/test. To prevent the /test/ directory from being labeled with the httpd_sys_content_t after running /sbin/restorecon, or after a file system relabel, run the following command as the Linux root user to delete the context from file_contexts.local:
/usr/sbin/semanage fcontext -d /test
/web(/.*)?, use quotation marks around the regular expression:
/usr/sbin/semanage fcontext -d "/web(/.*)?"
/usr/sbin/semanage.
/usr/sbin/semanage fcontext -a, use the full path to the file or directory to avoid files being mislabeled after a file system relabel, or after the /sbin/restorecon command is run.
file_t type. This should be the only use of this type, so that files without a context on disk can be distinguished in policy, and generally kept inaccessible to confined domains. The file_t type should not exist on correctly-labeled file systems, because all files on a system running SELinux should have an SELinux context, and the file_t type is never used in file-context configuration[9].
default_t type is used on files that do not match any other pattern in file-context configuration, so that such files can be distinguished from files that do not have a context on disk, and generally kept inaccessible to confined domains. If you create a new top-level directory, such as /mydirectory/, this directory may be labeled with the default_t type. If services need access to such a directory, update the file-contexts configuration for this location. Refer to Section 5.7.2, “Persistent Changes: semanage fcontext” for details on adding a context to the file-context configuration.
mount -o context command to override existing extended attributes, or to specify a different, default context for file systems that do not support extended attributes. This is useful if you do not trust a file system to supply the correct attributes, for example, removable media used in multiple systems. The mount -o context command can also be used to support labeling for file systems that do not support extended attributes, such as File Allocation Table (FAT) or NFS file systems. The context specified with the context is not written to disk: the original contexts are preserved, and are seen when mounting without a context option (if the file system had extended attributes in the first place).
mount -o context=SELinux_user:role:type:level command when mounting the desired file system. Context changes are not written to disk. By default, NFS mounts on the client side are labeled with a default context defined by policy for NFS file systems. In common policies, this default context uses the nfs_t type. Without additional mount options, this may prevent sharing NFS file systems via other services, such as the Apache HTTP Server. The following example mounts an NFS file system so that it can be shared via the Apache HTTP Server:
# mount server:/export /local/mount/point -o\ context="system_u:object_r:httpd_sys_content_t:s0"
-o context; however, since context changes are not written to disk for these situations, the context specified with the context option is only retained if the context option is used on the next mount, and if the same context is specified.
-o context, use the SELinux system_u user and object_r role, and concentrate on the type. If you are not using the MLS policy or multi-category security, use the s0 level.
context option, context changes (by users and processes) are prohibited. For example, running chcon on a file system mounted with a context option results in a Operation not supported error.
file_t type. If it is desirable to use a different default context, mount the file system with the defcontext option.
/dev/sda2) to the newly-created /test/ directory. It assumes that there are no rules in /etc/selinux/targeted/contexts/files/ that define a context for the /test/ directory:
# mount /dev/sda2 /test/ -o defcontext="system_u:object_r:samba_share_t:s0"
defcontext option defines that system_u:object_r:samba_share_t:s0 is "the default security context for unlabeled files"[10].
/test/) of the file system is treated as if it is labeled with the context specified by defcontext (this label is not stored on disk). This affects the labeling for files created under /test/: new files inherit the samba_share_t type, and these labels are stored on disk.
/test/ while the file system was mounted with a defcontext option retain their labels.
nfs_t type. Depending on policy configuration, services, such as Apache HTTP Server and MySQL, may not be able to read files labeled with the nfs_t type. This may prevent file systems labeled with this type from being mounted and then read or exported by other services.
context option when mounting to override the nfs_t type. Use the following context option to mount NFS file systems so that they can be shared via the Apache HTTP Server:
mount server:/export /local/mount/point -o\ context="system_u:object_r:httpd_sys_content_t:s0"
context option is only retained if the context option is used on the next mount, and if the same context is specified.
context options, Booleans can be turned on to allow services access to file systems labeled with the nfs_t type. Refer to Section 5.6.3, “Booleans for NFS and CIFS” for instructions on configuring Booleans to allow services access to the nfs_t type.
/export, which has two subdirectories, web/ and database/. The following commands attempt two mounts from a single NFS export, and try to override the context for each one:
# mount server:/export/web /local/web -o\ context="system_u:object_r:httpd_sys_content_t:s0" # mount server:/export/database /local/database -o\ context="system_u:object_r:mysqld_db_t:s0"
/var/log/messages:
kernel: SELinux: mount invalid. Same superblock, different security settings for (dev 0:15, type nfs)
-o nosharecache,context options. The following example mounts multiple mounts from a single NFS export, with a different context for each mount (allowing a single service access to each one):
# mount server:/export/web /local/web -o\ nosharecache,context="system_u:object_r:httpd_sys_content_t:s0" # mount server:/export/database /local/database -o\ nosharecache,context="system_u:object_r:mysqld_db_t:s0"
server:/export/web is mounted locally to /local/web/, with all files being labeled with the httpd_sys_content_t type, allowing Apache HTTP Server access. server:/export/database is mounted locally to /local/database, with all files being labeled with the mysqld_db_t type, allowing MySQL access. These type changes are not written to disk.
nosharecache options allows you to mount the same subdirectory of an export multiple times with different contexts (for example, mounting /export/web multiple times). Do not mount the same subdirectory from an export multiple times with different contexts, as this creates an overlapping mount, where files are accessible under two different contexts.
/etc/fstab or an automounter map, and use the desired context as a mount option. The following example adds an entry to /etc/fstab for an NFS context mount:
server:/export /local/mount/ nfs context="system_u:object_r:httpd_sys_content_t:s0" 0 0
user_home_t type:
$ touch file1 $ ls -Z file1 -rw-rw-r-- user1 group1 unconfined_u:object_r:user_home_t:s0 file1
/etc/, the new file is created in accordance to default-labeling rules for the /etc/ directory. Copying a file (without additional options) may not preserve the original context:
$ ls -Z file1 -rw-rw-r-- user1 group1 unconfined_u:object_r:user_home_t:s0 file1 # cp file1 /etc/ $ ls -Z /etc/file1 -rw-r--r-- root root unconfined_u:object_r:etc_t:s0 /etc/file1
file1 is copied to /etc/, if /etc/file1 does not exist, /etc/file1 is created as a new file. As shown in the example above, /etc/file1 is labeled with the etc_t type, in accordance to default-labeling rules.
cp options to preserve the context of the original file, such as --preserve=context. SELinux policy may prevent contexts from being preserved during copies.
cp command, if no options are given, the type is inherited from the targeted, parent directory:
$ touch file1 $ ls -Z file1 -rw-rw-r-- user1 group1 unconfined_u:object_r:user_home_t:s0 file1 $ ls -dZ /var/www/html/ drwxr-xr-x root root system_u:object_r:httpd_sys_content_t:s0 /var/www/html/ # cp file1 /var/www/html/ $ ls -Z /var/www/html/file1 -rw-r--r-- root root unconfined_u:object_r:httpd_sys_content_t:s0 /var/www/html/file1
file1 is created in a user's home directory, and is labeled with the user_home_t type. The /var/www/html/ directory is labeled with the httpd_sys_content_t type, as shown with the ls -dZ /var/www/html/ command. When file1 is copied to /var/www/html/, it inherits the httpd_sys_content_t type, as shown with the ls -Z /var/www/html/file1 command.
cp --preserve=context command to preserve contexts when copying:
$ touch file1 $ ls -Z file1 -rw-rw-r-- user1 group1 unconfined_u:object_r:user_home_t:s0 file1 $ ls -dZ /var/www/html/ drwxr-xr-x root root system_u:object_r:httpd_sys_content_t:s0 /var/www/html/ # cp --preserve=context file1 /var/www/html/ $ ls -Z /var/www/html/file1 -rw-r--r-- root root unconfined_u:object_r:user_home_t:s0 /var/www/html/file1
file1 is created in a user's home directory, and is labeled with the user_home_t type. The /var/www/html/ directory is labeled with the httpd_sys_content_t type, as shown with the ls -dZ /var/www/html/ command. Using the --preserve=context option preserves SELinux contexts during copy operations. As shown with the ls -Z /var/www/html/file1 command, the file1 user_home_t type was preserved when the file was copied to /var/www/html/.
cp -Z command to change the destination copy's context. The following example was performed in the user's home directory:
$ touch file1 $ cp -Z system_u:object_r:samba_share_t:s0 file1 file2 $ ls -Z file1 file2 -rw-rw-r-- user1 group1 unconfined_u:object_r:user_home_t:s0 file1 -rw-rw-r-- user1 group1 system_u:object_r:samba_share_t:s0 file2 $ rm file1 file2
-Z option. Without the -Z option, file2 would be labeled with the unconfined_u:object_r:user_home_t context.
# touch /etc/file1 # ls -Z /etc/file1 -rw-r--r-- root root unconfined_u:object_r:etc_t:s0 /etc/file1 # touch /tmp/file2 # ls -Z /tmp/file2 -rw-r--r-- root root unconfined_u:object_r:user_tmp_t:s0 /tmp/file2 # cp /tmp/file2 /etc/file1 # ls -Z /etc/file1 -rw-r--r-- root root unconfined_u:object_r:etc_t:s0 /etc/file1
/etc/file1, labeled with the etc_t type, and /tmp/file2, labeled with the user_tmp_t type. The cp /tmp/file2 /etc/file1 command overwrites file1 with file2. After copying, the ls -Z /etc/file1 command shows file1 labeled with the etc_t type, not the user_tmp_t type from /tmp/file2 that replaced /etc/file1.
/var/www/html/, which is used by the Apache HTTP Server. Since the file is moved, it does not inherit the correct SELinux context:
cd command without any arguments to change into your home directory. Once in your home directory, run the touch file1 command to create a file. This file is labeled with the user_home_t type:
$ ls -Z file1 -rw-rw-r-- user1 group1 unconfined_u:object_r:user_home_t:s0 file1
ls -dZ /var/www/html/ command to view the SELinux context of the /var/www/html/ directory:
$ ls -dZ /var/www/html/ drwxr-xr-x root root system_u:object_r:httpd_sys_content_t:s0 /var/www/html/
/var/www/html/ directory is labeled with the httpd_sys_content_t type. Files and directories created under the /var/www/html/ directory inherit this type, and as such, they are labeled with this type.
mv file1 /var/www/html/ command to move file1 to the /var/www/html/ directory. Since this file is moved, it keeps its current user_home_t type:
# mv file1 /var/www/html/ # ls -Z /var/www/html/file1 -rw-rw-r-- user1 group1 unconfined_u:object_r:user_home_t:s0 /var/www/html/file1
user_home_t type. If all files comprising a web page are labeled with the user_home_t type, or another type that the Apache HTTP Server can not read, permission is denied when attempting to access them via Firefox or text-based Web browsers.
mv command may result in the wrong SELinux context, preventing processes, such as the Apache HTTP Server and Samba, from accessing such files and directories.
/usr/sbin/matchpathcon command to check if files and directories have the correct SELinux context. From the matchpathcon(8) manual page: "matchpathcon queries the system policy and outputs the default security context associated with the file path."[11]. The following example demonstrates using the /usr/sbin/matchpathcon command to verify that files in /var/www/html/ directory are labeled correctly:
touch /var/www/html/file{1,2,3} command to create three files (file1, file2, and file3). These files inherit the httpd_sys_content_t type from the /var/www/html/ directory:
# touch /var/www/html/file{1,2,3}
# ls -Z /var/www/html/
-rw-r--r-- root root unconfined_u:object_r:httpd_sys_content_t:s0 file1
-rw-r--r-- root root unconfined_u:object_r:httpd_sys_content_t:s0 file2
-rw-r--r-- root root unconfined_u:object_r:httpd_sys_content_t:s0 file3
chcon -t samba_share_t /var/www/html/file1 command to change the file1 type to samba_share_t. Note: the Apache HTTP Server can not read files or directories labeled with the samba_share_t type.
/usr/sbin/matchpathcon -V option compares the current SELinux context to the correct, default context in SELinux policy. Run the /usr/sbin/matchpathcon -V /var/www/html/* command to check all files in the /var/www/html/ directory:
$ /usr/sbin/matchpathcon -V /var/www/html/* /var/www/html/file1 has context unconfined_u:object_r:samba_share_t:s0, should be system_u:object_r:httpd_sys_content_t:s0 /var/www/html/file2 verified. /var/www/html/file3 verified.
/usr/sbin/matchpathcon command explains that file1 is labeled with the samba_share_t type, but should be labeled with the httpd_sys_content_t type:
/var/www/html/file1 has context unconfined_u:object_r:samba_share_t:s0, should be system_u:object_r:httpd_sys_content_t:s0
file1, as the Linux root user, run the /sbin/restorecon -v /var/www/html/file1 command:
# /sbin/restorecon -v /var/www/html/file1 restorecon reset /var/www/html/file1 context unconfined_u:object_r:samba_share_t:s0->system_u:object_r:httpd_sys_content_t:s0
tar does not retain extended attributes by default. Since SELinux contexts are stored in extended attributes, contexts can be lost when archiving files. Use tar --selinux to create archives that retain contexts. If a Tar archive contains files without extended attributes, or if you want the extended attributes to match the system defaults, run the archive through /sbin/restorecon:
$ tar -xvf archive.tar | /sbin/restorecon -f -
/sbin/restorecon command.
touch /var/www/html/file{1,2,3} command to create three files (file1, file2, and file3). These files inherit the httpd_sys_content_t type from the /var/www/html/ directory:
# touch /var/www/html/file{1,2,3}
# ls -Z /var/www/html/
-rw-r--r-- root root unconfined_u:object_r:httpd_sys_content_t:s0 file1
-rw-r--r-- root root unconfined_u:object_r:httpd_sys_content_t:s0 file2
-rw-r--r-- root root unconfined_u:object_r:httpd_sys_content_t:s0 file3
cd /var/www/html/ command to change into the /var/www/html/ directory. Once in this directory, as the Linux root user, run the tar --selinux -cf test.tar file{1,2,3} command to create a Tar archive named test.tar.
mkdir /test command to create a new directory, and then, run the chmod 777 /test/ command to allow all users full-access to the /test/ directory.
cp /var/www/html/test.tar /test/ command to copy the test.tar file in to the /test/ directory.
cd /test/ command to change into the /test/ directory. Once in this directory, run the tar -xvf test.tar command to extract the Tar archive.
ls -lZ /test/ command to view the SELinux contexts. The httpd_sys_content_t type has been retained, rather than being changed to default_t, which would have happened had the --selinux not been used:
$ ls -lZ /test/ -rw-r--r-- user1 group1 unconfined_u:object_r:httpd_sys_content_t:s0 file1 -rw-r--r-- user1 group1 unconfined_u:object_r:httpd_sys_content_t:s0 file2 -rw-r--r-- user1 group1 unconfined_u:object_r:httpd_sys_content_t:s0 file3 -rw-r--r-- user1 group1 unconfined_u:object_r:default_t:s0 test.tar
/test/ directory is no longer required, as the Linux root user, run the rm -ri /test/ command to remove it, as well as all files in it.
tar, such as the --xattrs option that retains all extended attributes.
star does not retain extended attributes by default. Since SELinux contexts are stored in extended attributes, contexts can be lost when archiving files. Use star -xattr -H=exustar to create archives that retain contexts. The star package is not installed by default. To install star, run the yum install star command as the Linux root user.
touch /var/www/html/file{1,2,3} command to create three files (file1, file2, and file3). These files inherit the httpd_sys_content_t type from the /var/www/html/ directory:
# touch /var/www/html/file{1,2,3}
# ls -Z /var/www/html/
-rw-r--r-- root root unconfined_u:object_r:httpd_sys_content_t:s0 file1
-rw-r--r-- root root unconfined_u:object_r:httpd_sys_content_t:s0 file2
-rw-r--r-- root root unconfined_u:object_r:httpd_sys_content_t:s0 file3
cd /var/www/html/ command to change into the /var/www/html/ directory. Once in this directory, as the Linux root user, run the star -xattr -H=exustar -c -f=test.star file{1,2,3} command to create a Star archive named test.star:
# star -xattr -H=exustar -c -f=test.star file{1,2,3}
star: 1 blocks + 0 bytes (total of 10240 bytes = 10.00k).
mkdir /test command to create a new directory, and then, run the chmod 777 /test/ command to allow all users full-access to the /test/ directory.
cp /var/www/html/test.star /test/ command to copy the test.star file in to the /test/ directory.
cd /test/ command to change into the /test/ directory. Once in this directory, run the star -x -f=test.star command to extract the Star archive:
$ star -x -f=test.star star: 1 blocks + 0 bytes (total of 10240 bytes = 10.00k).
ls -lZ /test/ command to view the SELinux contexts. The httpd_sys_content_t type has been retained, rather than being changed to default_t, which would have happened had the --selinux not been used:
$ ls -lZ /test/ -rw-r--r-- user1 group1 unconfined_u:object_r:httpd_sys_content_t:s0 file1 -rw-r--r-- user1 group1 unconfined_u:object_r:httpd_sys_content_t:s0 file2 -rw-r--r-- user1 group1 unconfined_u:object_r:httpd_sys_content_t:s0 file3 -rw-r--r-- user1 group1 unconfined_u:object_r:default_t:s0 test.star
/test/ directory is no longer required, as the Linux root user, run the rm -ri /test/ command to remove it, as well as all files in it.
star is no longer required, as the Linux root user, run the yum remove star command to remove the package.
star.
/selinux/avc/cache_stats, and you can specify a different cache file with the -f /path/to/file option.
[root@localhost ~]# avcstat lookups hits misses allocs reclaims frees 47517410 47504630 12780 12780 12176 12275
seinfo is a command line utility that uses either the policy.conf file or a binary policy file as input.
seinfo will vary between binary and source files. For example, the policy source file uses the { } brackets to group multiple rule elements onto a single line. A similar effect happens with attributes, where a single attribute expands into one or many types. Because these are expanded and no longer relevant in the binary policy file, they have a return value of zero in the search results. However, the number of rules greatly increases as each formerly one line rule using brackets is now a number of individual lines.
[root@localhost ]# seinfo Statistics for policy file: /etc/selinux/targeted/policy/policy.24 Policy Version & Type: v.24 (binary, mls) Classes: 77 Permissions: 229 Sensitivities: 1 Categories: 1024 Types: 3001 Attributes: 244 Users: 9 Roles: 13 Booleans: 158 Cond. Expr.: 193 Allow: 262796 Neverallow: 0 Auditallow: 44 Dontaudit: 156710 Type_trans: 10760 Type_change: 38 Type_member: 44 Role allow: 20 Role_trans: 237 Range_trans: 2546 Constraints: 62 Validatetrans: 0 Initial SIDs: 27 Fs_use: 22 Genfscon: 82 Portcon: 373 Netifcon: 0 Nodecon: 0 Permissives: 22 Polcap: 2 [root@localhost ]#
seinfo command can also list the number of types with the domain attribute, giving an estimate of the number of different confined processes:
# seinfo -adomain -x | wc -l 550
# seinfo -aunconfined_domain_type -x | wc -l 52
--permissive option.
# seinfo --permissive -x | wc -l 31
| wc -l option in the above commands to see the full lists.
[scott@localhost ~]$ sesearch --role_allow -t httpd_sys_content_t \/etc/selinux/targeted/policy/policy.24 Found 20 role allow rules: allow system_r sysadm_r; allow sysadm_r system_r; allow sysadm_r staff_r; allow sysadm_r user_r; allow system_r git_shell_r; allow system_r guest_r; allow logadm_r system_r; allow system_r logadm_r; allow system_r nx_server_r; allow system_r staff_r; allow staff_r logadm_r; allow staff_r sysadm_r; allow staff_r unconfined_r; allow staff_r webadm_r; allow unconfined_r system_r; allow system_r unconfined_r; allow system_r user_r; allow webadm_r system_r; allow system_r webadm_r; allow system_r xguest_r;
sesearch command can provide the number of allow rules:
# sesearch --allow | wc -l 262798
# sesearch --dontaudit | wc -l 156712
[8] Brindle, Joshua. "Re: blurb for fedora setools packages" Email to Murray McAllister. 1 November 2008. Any edits or changes in this version were done by Murray McAllister.
[9]
Files in /etc/selinux/targeted/contexts/files/ define contexts for files and directories. Files in this directory are read by restorecon and setfiles to restore files and directories to their default contexts.
[10] Morris, James. "Filesystem Labeling in SELinux". Published 1 October 2004. Accessed 14 October 2008: http://www.linuxjournal.com/article/7426.
[11] The matchpathcon(8) manual page, as shipped with the libselinux-utils package in Red Hat Enterprise Linux, is written by Daniel Walsh. Any edits or changes in this version were done by Murray McAllister.
su and sudo commands. This helps protect the system from the user. Refer to Section 4.3, “Confined and Unconfined Users” for further information about confined users.
semanage login -l command to view the mapping between Linux users and SELinux users:
# /usr/sbin/semanage login -l Login Name SELinux User MLS/MCS Range __default__ unconfined_u s0-s0:c0.c1023 root unconfined_u s0-s0:c0.c1023 system_u system_u s0-s0:c0.c1023
__default__ login by default (which is in turn mapped to the SELinux unconfined_u user). When a Linux user is created with the useradd command, if no options are specified, they are mapped to the SELinux unconfined_u user. The following defines the default-mapping:
__default__ unconfined_u s0-s0:c0.c1023
unconfined_u user run in the unconfined_t domain. This is seen by running the id -Z command while logged-in as a Linux user mapped to unconfined_u:
$ id -Z unconfined_u:unconfined_r:unconfined_t:s0-s0:c0.c1023
unconfined_t domain, SELinux policy rules are applied, but policy rules exist that allow Linux users running in the unconfined_t domain almost all access. If unconfined Linux users execute an application that SELinux policy defines can transition from the unconfined_t domain to its own confined domain, unconfined Linux users are still subject to the restrictions of that confined domain. The security benefit of this is that, even though a Linux user is running unconfined, the application remains confined, and therefore, the exploitation of a flaw in the application can be limited by policy. Note: this does not protect the system from the user. Instead, the user and the system are being protected from possible damage caused by a flaw in the application.
useradd, use the -Z option to specify which SELinux user they are mapped to. The following example creates a new Linux user, useruuser, and maps that user to the SELinux user_u user. Linux users mapped to the SELinux user_u user run in the user_t domain. In this domain, Linux users are unable to run setuid applications unless SELinux policy permits it (such as passwd), and can not run su or sudo, preventing them from becoming the Linux root user with these commands.
/usr/sbin/useradd -Z user_u useruuser command to create a new Linux user (useruuser) that is mapped to the SELinux user_u user.
semanage login -l command to view the mapping between the Linux useruuser user and user_u:
# /usr/sbin/semanage login -l Login Name SELinux User MLS/MCS Range __default__ unconfined_u s0-s0:c0.c1023 root unconfined_u s0-s0:c0.c1023 system_u system_u s0-s0:c0.c1023 useruuser user_u s0
passwd useruuser command to assign a password to the Linux useruuser user:
# passwd useruuser Changing password for user useruuser. New UNIX password:Enter a passwordRetype new UNIX password:Enter the same password againpasswd: all authentication tokens updated successfully.
user_u), and sets up the resulting SELinux context. The Linux user's shell is then launched with this context. Run the id -Z command to view the context of a Linux user:
[useruuser@localhost ~]$ id -Z user_u:user_r:user_t:s0
/usr/sbin/userdel -r useruuser command as the Linux root user to remove it, along with its home directory.
unconfined_u user (the default behavior), and you would like to change which SELinux user they are mapped to, use the semanage login command. The following example creates a new Linux user named newuser, then maps that Linux user to the SELinux user_u user:
/usr/sbin/useradd newuser command to create a new Linux user (newuser). Since this user uses the default mapping, it does not appear in the /usr/sbin/semanage login -l output:
# /usr/sbin/semanage login -l Login Name SELinux User MLS/MCS Range __default__ unconfined_u s0-s0:c0.c1023 root unconfined_u s0-s0:c0.c1023 system_u system_u s0-s0:c0.c1023
user_u user, run the following command as the Linux root user:
/usr/sbin/semanage login -a -s user_u newuser
-a option adds a new record, and the -s option specifies the SELinux user to map a Linux user to. The last argument, newuser, is the Linux user you want mapped to the specified SELinux user.
user_u, run the semanage login -l command as the Linux root user:
# /usr/sbin/semanage login -l Login Name SELinux User MLS/MCS Range __default__ unconfined_u s0-s0:c0.c1023 newuser user_u s0 root unconfined_u s0-s0:c0.c1023 system_u system_u s0-s0:c0.c1023
passwd newuser command to assign a password to the Linux newuser user:
# passwd newuser Changing password for user newuser. New UNIX password:Enter a passwordRetype new UNIX password:Enter the same password againpasswd: all authentication tokens updated successfully.
id -Z command to view the newuser's SELinux context:
[newuser@rlocalhost ~]$ id -Z user_u:user_r:user_t:s0
userdel -r newuser command as the Linux root user to remove it, along with its home directory. Also, the mapping between the Linux newuser user and user_u is removed:
# /usr/sbin/userdel -r newuser # /usr/sbin/semanage login -l Login Name SELinux User MLS/MCS Range __default__ unconfined_u s0-s0:c0.c1023 root unconfined_u s0-s0:c0.c1023 system_u system_u s0-s0:c0.c1023
__default__ login by default (which is in turn mapped to the SELinux unconfined_u user). If you would like new Linux users, and Linux users not specifically mapped to an SELinux user to be confined by default, change the default mapping with the semanage login command.
unconfined_u to user_u:
/usr/sbin/semanage login -m -S targeted -s "user_u" -r s0 __default__
semanage login -l command as the Linux root user to verify the __default__ login is mapped to user_u:
# /usr/sbin/semanage login -l Login Name SELinux User MLS/MCS Range __default__ user_u s0 root unconfined_u s0-s0:c0.c1023 system_u system_u s0-s0:c0.c1023
semanage login -l output, they are mapped to user_u, as per the __default__ login.
__default__ login to the SELinux unconfined_u user:
/usr/sbin/semanage login -m -S targeted -s "unconfined_u" -r\ s0-s0:c0.c1023 __default__
yum install xguest command to install the xguest package. Install dependencies as required.
getenforce command to confirm that SELinux is running in enforcing mode:
$ /usr/sbin/getenforce Enforcing
Guest account is added to the GDM login screen.
/tmp/, which they have write access to, helps prevent flawed or malicious applications from modifying files that users own. In Red Hat Enterprise Linux 6, by default, Linux users in the guest_t and xguest_t domains can not execute applications in their home directories or /tmp/; however, by default, Linux users in the user_t and staff_t domains can.
setsebool command. The setsebool command must be run as the Linux root user. The setsebool -P command makes persistent changes. Do not use the -P option if you do not want changes to persist across reboots:
guest_t domain to execute applications in their home directories and /tmp/:
/usr/sbin/setsebool -P allow_guest_exec_content on
xguest_t domain to execute applications in their home directories and /tmp/:
/usr/sbin/setsebool -P allow_xguest_exec_content on
user_t domain from executing applications in their home directories and /tmp/:
/usr/sbin/setsebool -P allow_user_exec_content off
staff_t domain from executing applications in their home directories and /tmp/:
/usr/sbin/setsebool -P allow_staff_exec_content off
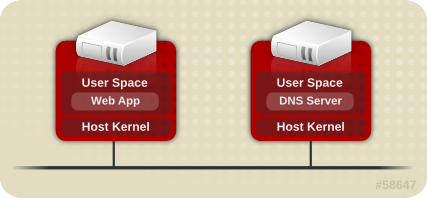

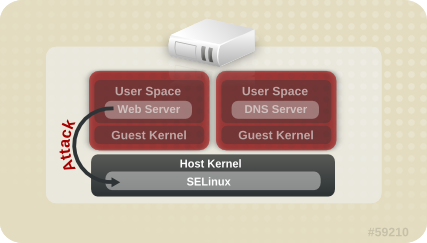
# ps -eZ | grep qemu system_u:system_r:svirt_t:s0:c87,c520 27950 ? 00:00:17 qemu-kvm system_u:system_r:svirt_t:s0:c639,c757 27989 ? 00:00:06 qemu-system-x86
# ls -lZ /var/lib/libvirt/images/* system_u:object_r:svirt_image_t:s0:c87,c520 image1
| Type | SELinux Context | Description |
|---|---|---|
| Virtual Machine Processes | system_u:system_r:svirt_t:MCS1 | MCS1 is a randomly selected MCS field. Currently approximately 500,000 labels are supported. |
| Virtual Machine Image | system_u:object_r:svirt_image_t:MCS1 | Only svirt_t processes with the same MCS fields are able to read/write these image files and devices. |
| Virtual Machine Shared Read/Write Content | system_u:object_r:svirt_image_t:s0 | All svirt_t processes are allowed to write to the svirt_image_t:s0 files and devices. |
| Virtual Machine Shared Shared Read Only content | system_u:object_r:svirt_content_t:s0 | All svirt_t processes are able to read files/devices with this label. |
| Virtual Machine Image | system_u:object_r:virt_content_t:s0 | System default label used when an image exits. No svirt_t virtual processes are allowed to read files/devices with this label. |
audit2allow.
| Daemon | Log Location |
|---|---|
| auditd on | /var/log/audit/audit.log |
| auditd off; rsyslogd on | /var/log/messages |
| setroubleshootd, rsyslogd, and auditd on | /var/log/audit/audit.log. Easier-to-read denial messages also sent to /var/log/messages |
setroubleshootd and auditd daemons are running, a warning is displayed when access is denied by SELinux:
Forbidden
You don't have permission to access file name on this server
/var/log/messages and /var/log/audit/audit.log for "SELinux is preventing" and "denied" errors respectively. This can be done by running the following commands as the Linux root user:
grep "SELinux is preventing" /var/log/messages
grep "denied" /var/log/audit/audit.log
/var/www/html/ for a website, an administrator wants to use /srv/myweb/. On Red Hat Enterprise Linux 6, the /srv/ directory is labeled with the var_t type. Files and directories created and /srv/ inherit this type. Also, newly-created top-level directories (such as /myserver/) may be labeled with the default_t type. SELinux prevents the Apache HTTP Server (httpd) from accessing both of these types. To allow access, SELinux must know that the files in /srv/myweb/ are to be accessible to httpd:
# /usr/sbin/semanage fcontext -a -t httpd_sys_content_t \ "/srv/myweb(/.*)?"
semanage command adds the context for the /srv/myweb/ directory (and all files and directories under it) to the SELinux file-context configuration[12]. The semanage command does not change the context. As the Linux root user, run the restorecon command to apply the changes:
# /sbin/restorecon -R -v /srv/myweb
matchpathcon command checks the context of a file path and compares it to the default label for that path. The following example demonstrates using matchpathcon on a directory that contains incorrectly labeled files:
$ /usr/sbin/matchpathcon -V /var/www/html/* /var/www/html/index.html has context unconfined_u:object_r:user_home_t:s0, should be system_u:object_r:httpd_sys_content_t:s0 /var/www/html/page1.html has context unconfined_u:object_r:user_home_t:s0, should be system_u:object_r:httpd_sys_content_t:s0
index.html and page1.html files are labeled with the user_home_t type. This type is used for files in user home directories. Using the mv command to move files from your home directory may result in files being labeled with the user_home_t type. This type should not exist outside of home directories. Use the restorecon command to restore such files to their correct type:
# /sbin/restorecon -v /var/www/html/index.html restorecon reset /var/www/html/index.html context unconfined_u:object_r:user_home_t:s0->system_u:object_r:httpd_sys_content_t:s0
-R option:
# /sbin/restorecon -R -v /var/www/html/ restorecon reset /var/www/html/page1.html context unconfined_u:object_r:samba_share_t:s0->system_u:object_r:httpd_sys_content_t:s0 restorecon reset /var/www/html/index.html context unconfined_u:object_r:samba_share_t:s0->system_u:object_r:httpd_sys_content_t:s0
matchpathcon.
semanage command.
httpd_can_network_connect_db Boolean on:
# /usr/sbin/setsebool -P httpd_can_network_connect_db on
getsebool and grep commands to see if any Booleans are available to allow access. For example, use the getsebool -a | grep ftp command to search for FTP related Booleans:
$ /usr/sbin/getsebool -a | grep ftp allow_ftpd_anon_write --> off allow_ftpd_full_access --> off allow_ftpd_use_cifs --> off allow_ftpd_use_nfs --> off ftp_home_dir --> off httpd_enable_ftp_server --> off tftp_anon_write --> off
/usr/sbin/getsebool -a command. For a list of Booleans, an explanation of what each one is, and whether they are on or off, run the /usr/sbin/semanage boolean -l command as the Linux root user. Refer to Section 5.6, “Booleans” for information about listing and configuring Booleans.
semanage port -l | grep http command as the Linux root user to list http related ports:
# /usr/sbin/semanage port -l | grep http http_cache_port_t tcp 3128, 8080, 8118 http_cache_port_t udp 3130 http_port_t tcp 80, 443, 488, 8008, 8009, 8443 pegasus_http_port_t tcp 5988 pegasus_https_port_t tcp 5989
http_port_t port type defines the ports Apache HTTP Server can listen on, which in this case, are TCP ports 80, 443, 488, 8008, 8009, and 8443. If an administrator configures httpd.conf so that httpd listens on port 9876 (Listen 9876), but policy is not updated to reflect this, the service httpd start command fails:
# /sbin/service httpd start Starting httpd: (13)Permission denied: make_sock: could not bind to address [::]:9876 (13)Permission denied: make_sock: could not bind to address 0.0.0.0:9876 no listening sockets available, shutting down Unable to open logs [FAILED]
/var/log/audit/audit.log:
type=AVC msg=audit(1225948455.061:294): avc: denied { name_bind } for pid=4997 comm="httpd" src=9876 scontext=unconfined_u:system_r:httpd_t:s0 tcontext=system_u:object_r:port_t:s0 tclass=tcp_socket
httpd to listen on a port that is not listed for the http_port_t port type, run the semanage port command to add a port to policy configuration[13]:
# /usr/sbin/semanage port -a -t http_port_t -p tcp 9876
-a option adds a new record; the -t option defines a type; and the -p option defines a protocol. The last argument is the port number to add.
audit2allow to create a custom policy module to allow access. Refer to Section 8.3.8, “Allowing Access: audit2allow” for information about using audit2allow.
audit2allow.
ls -l command to view the standard Linux permissions:
$ ls -l /var/www/html/index.html -rw-r----- 1 root root 0 2009-05-07 11:06 index.html
index.html is owned by the root user and group. The root user has read and write permissions (-rw), and members of the root group have read permissions (-r-). Everyone else has no access (---). By default, such permissions do not allow httpd to read this file. To resolve this issue, use the chown command to change the owner and group. This command must be run as the Linux root user:
# chown apache:apache /var/www/html/index.html
httpd runs as the Linux apache user. If you run httpd with a different user, replace apache:apache with that user.
dontaudit rules. These rules are common in standard policy. The downside of dontaudit is that, although SELinux denies access, denial messages are not logged, making troubleshooting hard.
dontaudit rules, allowing all denials to be logged, run the following command as the Linux root user:
/usr/sbin/semodule -DB
-D option disables dontaudit rules; the -B option rebuilds policy. After running semodule -DB, try exercising the application that was encountering permission problems, and see if SELinux denials — relevant to the application — are now being logged. Take care in deciding which denials should be allowed, as some should be ignored and handled via dontaudit rules. If in doubt, or in search of guidance, contact other SELinux users and developers on an SELinux list, such as fedora-selinux-list.
dontaudit rules, run the following command as the Linux root user:
/usr/sbin/semodule -B
dontaudit rules, run the sesearch --dontaudit command. Narrow down searches using the -s domain option and the grep command. For example:
$ sesearch --dontaudit -s smbd_t | grep squid WARNING: This policy contained disabled aliases; they have been removed. dontaudit smbd_t squid_port_t : tcp_socket name_bind ; dontaudit smbd_t squid_port_t : udp_socket name_bind ;
httpd accessing NFS file systems). This information may be in the standard manual page, or a manual page with selinux prepended or appended.
samba_share_t type, as well as Booleans to allow files labeled with types other than samba_share_t to be exported via Samba.
nfs_export_all_ro or nfs_export_all_rw must be turned on.
Red Hat SELinux BIND Security Profile section). The named_selinux(8) manual page describes that, by default, named can not write to master zone files, and to allow such access, the named_write_master_zones Boolean must be turned on.
domain_disable_transinitrc_t. Turning such Booleans on can cause major problems. For example, if the httpd_disable_trans Boolean is turned on:
httpd runs in the unconfined initrc_t domain. Files created by processes running in the initrc_t domain may not have the same labeling rules applied as files created by a process running in the httpd_t domain, potentially allowing processes to create mislabeled files. This causes access problems later on.
httpd_t can not communicate with initrc_t, possibly causing additional failures.
audit2allow could then be used to help write the policy. This put the whole system at risk. With permissive domains, only the domain in the new policy can be marked permissive, without putting the whole system at risk.
semanage permissive -a domain command, where domain is the domain you want to make permissive. For example, run the following command as the Linux root user to make the httpd_t domain (the domain the Apache HTTP Server runs in) permissive:
/usr/sbin/semanage permissive -a httpd_t
semodule -l | grep permissive command as the Linux root user. For example:
# /usr/sbin/semodule -l | grep permissive permissive_httpd_t 1.0
semanage permissive -d domain command as the Linux root user. For example:
/usr/sbin/semanage permissive -d httpd_t
SYSCALL message is different for permissive domains. The following is an example AVC denial (and the associated system call) from the Apache HTTP Server:
type=AVC msg=audit(1226882736.442:86): avc: denied { getattr } for pid=2427 comm="httpd" path="/var/www/html/file1" dev=dm-0 ino=284133 scontext=unconfined_u:system_r:httpd_t:s0 tcontext=unconfined_u:object_r:samba_share_t:s0 tclass=file
type=SYSCALL msg=audit(1226882736.442:86): arch=40000003 syscall=196 success=no exit=-13 a0=b9a1e198 a1=bfc2921c a2=54dff4 a3=2008171 items=0 ppid=2425 pid=2427 auid=502 uid=48 gid=48 euid=48 suid=48 fsuid=48 egid=48 sgid=48 fsgid=48 tty=(none) ses=4 comm="httpd" exe="/usr/sbin/httpd" subj=unconfined_u:system_r:httpd_t:s0 key=(null)
httpd_t domain is not permissive, and as such, the action is denied, and the SYSCALL message contains success=no. The following is an example AVC denial for the same situation, except the semanage permissive -a httpd_t command has been run to make the httpd_t domain permissive:
type=AVC msg=audit(1226882925.714:136): avc: denied { read } for pid=2512 comm="httpd" name="file1" dev=dm-0 ino=284133 scontext=unconfined_u:system_r:httpd_t:s0 tcontext=unconfined_u:object_r:samba_share_t:s0 tclass=file
type=SYSCALL msg=audit(1226882925.714:136): arch=40000003 syscall=5 success=yes exit=11 a0=b962a1e8 a1=8000 a2=0 a3=8000 items=0 ppid=2511 pid=2512 auid=502 uid=48 gid=48 euid=48 suid=48 fsuid=48 egid=48 sgid=48 fsgid=48 tty=(none) ses=4 comm="httpd" exe="/usr/sbin/httpd" subj=unconfined_u:system_r:httpd_t:s0 key=(null)
success=yes in the SYSCALL message.
auditd, rsyslogd, and setroubleshootd daemons are running. Refer to Section 5.2, “Which Log File is Used” for information about starting these daemons. A number of tools are available for searching for and viewing SELinux denials, such as ausearch, aureport, and sealert.
ausearch. From the ausearch(8) manual page: "ausearch is a tool that can query the audit daemon logs based for events based on different search criteria"[14]. The ausearch tool accesses /var/log/audit/audit.log, and as such, must be run as the Linux root user:
| Searching For | Command |
|---|---|
| all denials | /sbin/ausearch -m avc |
| denials for that today | /sbin/ausearch -m avc -ts today |
| denials from the last 10 minutes | /sbin/ausearch -m avc -ts recent |
-c comm-name option, where comm-name "is the executable’s name"[15], for example, httpd for the Apache HTTP Server, and smbd for Samba:
/sbin/ausearch -m avc -c httpd
/sbin/ausearch -m avc -c smbd
ausearch options.
aureport. From the aureport(8) manual page: "aureport is a tool that produces summary reports of the audit system logs"[16]. The aureport tool accesses /var/log/audit/audit.log, and as such, must be run as the Linux root user. To view a list of SELinux denials and how often each one occurred, run the aureport -a command. The following is example output that includes two denials:
# /sbin/aureport -a AVC Report ======================================================== # date time comm subj syscall class permission obj event ======================================================== 1. 05/01/2009 21:41:39 httpd unconfined_u:system_r:httpd_t:s0 195 file getattr system_u:object_r:samba_share_t:s0 denied 2 2. 05/03/2009 22:00:25 vsftpd unconfined_u:system_r:ftpd_t:s0 5 file read unconfined_u:object_r:cifs_t:s0 denied 4
aureport options.
sealert, which reads denial messages translated by setroubleshoot-server. Denials are assigned IDs, as seen in /var/log/messages. The following is an example denial from messages:
setroubleshoot: SELinux is preventing httpd (httpd_t) "getattr" to /var/www/html/file1 (samba_share_t). For complete SELinux messages. run sealert -l 84e0b04d-d0ad-4347-8317-22e74f6cd020
84e0b04d-d0ad-4347-8317-22e74f6cd020. The -l option takes an ID as an argument. Running the sealert -l 84e0b04d-d0ad-4347-8317-22e74f6cd020 command presents a detailed analysis of why SELinux denied access, and a possible solution for allowing access.
setroubleshootd, dbus and auditd daemons are running, a warning is displayed when access is denied by SELinux. Clicking on 'Show' launches the sealert GUI, and displays denials in HTML output:
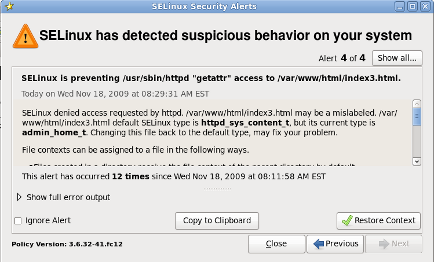
sealert -b command to launch the sealert GUI.
sealert -l \* command to view a detailed analysis of all denials.
sealert -a /var/log/audit/audit.log -H > audit.html command to create a HTML version of the sealert analysis, as seen with the sealert GUI.
sealert options.
/var/log/audit/audit.log. The following is an example AVC denial (and the associated system call) that occurred when the Apache HTTP Server (running in the httpd_t domain) attempted to access the /var/www/html/file1 file (labeled with the samba_share_t type):
type=AVC msg=audit(1226874073.147:96): avc: denied { getattr } for pid=2465 comm="httpd" path="/var/www/html/file1" dev=dm-0 ino=284133 scontext=unconfined_u:system_r:httpd_t:s0 tcontext=unconfined_u:object_r:samba_share_t:s0 tclass=file
type=SYSCALL msg=audit(1226874073.147:96): arch=40000003 syscall=196 success=no exit=-13 a0=b98df198 a1=bfec85dc a2=54dff4 a3=2008171 items=0 ppid=2463 pid=2465 auid=502 uid=48 gid=48 euid=48 suid=48 fsuid=48 egid=48 sgid=48 fsgid=48 tty=(none) ses=6 comm="httpd" exe="/usr/sbin/httpd" subj=unconfined_u:system_r:httpd_t:s0 key=(null)
{ getattr }getattr indicates the source process was trying to read the target file's status information. This occurs before reading files. This action is denied due to the file being accessed having the wrong label. Commonly seen permissions include getattr, read, and write.
httpd"exe= section of the system call (SYSCALL) message, which in this case, is exe="/usr/sbin/httpd".
/var/www/html/file1"unconfined_u:system_r:httpd_t:s0"httpd_t domain.
unconfined_u:object_r:samba_share_t:s0"file1. Note: the samba_share_t type is not accessible to processes running in the httpd_t domain.
tcontext may match the scontext, for example, when a process attempts to execute a system service that will change characteristics of that running process, such as the user ID. Also, the tcontext may match the scontext when a process tries to use more resources (such as memory) than normal limits allow, resulting in a security check to see if that process is allowed to break those limits.
SYSCALL) message, two items are of interest:
success=no: indicates whether the denial (AVC) was enforced or not. success=no indicates the system call was not successful (SELinux denied access). success=yes indicates the system call was successful - this can be seen for permissive domains or unconfined domains, such as initrc_t and kernel_t.
exe="/usr/sbin/httpd": the full path to the executable that launched the process, which in this case, is exe="/usr/sbin/httpd".
scontext) with the target context (tcontext). Should the process (scontext) be accessing such an object (tcontext)? For example, the Apache HTTP Server (httpd_t) should only be accessing types specified in the httpd_selinux(8) manual page, such as httpd_sys_content_t, public_content_t, and so on, unless configured otherwise.
/var/log/messages. The following is an example AVC denial (logged to messages) that occurred when the Apache HTTP Server (running in the httpd_t domain) attempted to access the /var/www/html/file1 file (labeled with the samba_share_t type):
hostname setroubleshoot: SELinux is preventing httpd (httpd_t) "getattr" to /var/www/html/file1 (samba_share_t). For complete SELinux messages. run sealert -l 84e0b04d-d0ad-4347-8317-22e74f6cd020
sealert -l 84e0b04d-d0ad-4347-8317-22e74f6cd020 command to view the complete message. This command only works on the local machine, and presents the same information as the sealert GUI:
$ sealert -l 84e0b04d-d0ad-4347-8317-22e74f6cd020 Summary: SELinux is preventing httpd (httpd_t) "getattr" to /var/www/html/file1 (samba_share_t). Detailed Description: SELinux denied access to /var/www/html/file1 requested by httpd. /var/www/html/file1 has a context used for sharing by different program. If you would like to share /var/www/html/file1 from httpd also, you need to change its file context to public_content_t. If you did not intend to this access, this could signal a intrusion attempt. Allowing Access: You can alter the file context by executing chcon -t public_content_t '/var/www/html/file1' Fix Command: chcon -t public_content_t '/var/www/html/file1' Additional Information: Source Context unconfined_u:system_r:httpd_t:s0 Target Context unconfined_u:object_r:samba_share_t:s0 Target Objects /var/www/html/file1 [ file ] Source httpd Source Path /usr/sbin/httpd Port <Unknown> HosthostnameSource RPM Packages httpd-2.2.10-2 Target RPM Packages Policy RPM selinux-policy-3.5.13-11.fc12 Selinux Enabled True Policy Type targeted MLS Enabled True Enforcing Mode Enforcing Plugin Name public_content Host NamehostnamePlatformLinux hostname 2.6.27.4-68.fc12.i686 #1 SMP Thu Oct30 00:49:42 EDT 2008 i686 i686 Alert Count 4 First Seen Wed Nov 5 18:53:05 2008 Last Seen Wed Nov 5 01:22:58 2008 Local ID 84e0b04d-d0ad-4347-8317-22e74f6cd020 Line Numbers Raw Audit Messages node=hostnametype=AVC msg=audit(1225812178.788:101): avc: denied { getattr } for pid=2441 comm="httpd" path="/var/www/html/file1" dev=dm-0 ino=284916 scontext=unconfined_u:system_r:httpd_t:s0 tcontext=unconfined_u:object_r:samba_share_t:s0 tclass=file node=hostnametype=SYSCALL msg=audit(1225812178.788:101): arch=40000003 syscall=196 success=no exit=-13 a0=b8e97188 a1=bf87aaac a2=54dff4 a3=2008171 items=0 ppid=2439 pid=2441 auid=502 uid=48 gid=48 euid=48 suid=48 fsuid=48 egid=48 sgid=48 fsgid=48 tty=(none) ses=3 comm="httpd" exe="/usr/sbin/httpd" subj=unconfined_u:system_r:httpd_t:s0 key=(null)
/var/log/messages. In this example, the httpd process was denied access to a file (file1), which is labeled with the samba_share_t type.
file1 is labeled with the samba_share_t type. This type is used for files and directories that you want to export via Samba. The description suggests changing the type to a type that can be accessed by the Apache HTTP Server and Samba, if such access is desired.
file1 type to public_content_t, which is accessible to the Apache HTTP Server and Samba.
selinux-policy-3.5.13-11.fc12), but may not help towards solving why the denial occurred.
/var/log/audit/audit.log that are associated with the denial. Refer to Section 8.3.6, “Raw Audit Messages” for information about each item in the AVC denial.
audit2allow.
audit2allow - generate SELinux policy allow rules from logs of denied operations"[17]. After analyzing denials as per Section 8.3.7, “sealert Messages”, and if no label changes or Booleans allowed access, use audit2allow to create a local policy module. After access is denied by SELinux, running the audit2allow command presents Type Enforcement rules that allow the previously denied access.
audit2allow to create a policy module:
/var/log/audit/audit.log:
type=AVC msg=audit(1226270358.848:238): avc: denied { write } for pid=13349 comm="certwatch" name="cache" dev=dm-0 ino=218171 scontext=system_u:system_r:certwatch_t:s0 tcontext=system_u:object_r:var_t:s0 tclass=dir
type=SYSCALL msg=audit(1226270358.848:238): arch=40000003 syscall=39 success=no exit=-13 a0=39a2bf a1=3ff a2=3a0354 a3=94703c8 items=0 ppid=13344 pid=13349 auid=4294967295 uid=0 gid=0 euid=0 suid=0 fsuid=0 egid=0 sgid=0 fsgid=0 tty=(none) ses=4294967295 comm="certwatch" exe="/usr/bin/certwatch" subj=system_u:system_r:certwatch_t:s0 key=(null)
comm="certwatch") was denied write access ({ write }) to a directory labeled with the var_t type (tcontext=system_u:object_r:var_t:s0). Analyze the denial as per Section 8.3.7, “sealert Messages”. If no label changes or Booleans allowed access, use audit2allow to create a local policy module.
certwatch denial in step 1, run the audit2allow -w -a command to produce a human-readable description of why access was denied. The -a option causes all audit logs to be read. The -w option produces the human-readable description. The audit2allow tool accesses /var/log/audit/audit.log, and as such, must be run as the Linux root user:
# audit2allow -w -a
type=AVC msg=audit(1226270358.848:238): avc: denied { write } for pid=13349 comm="certwatch" name="cache" dev=dm-0 ino=218171 scontext=system_u:system_r:certwatch_t:s0 tcontext=system_u:object_r:var_t:s0 tclass=dir
Was caused by:
Missing type enforcement (TE) allow rule.
You can use audit2allow to generate a loadable module to allow this access.
audit2allow -a command to view the Type Enforcement rule that allows the denied access:
# audit2allow -a #============= certwatch_t ============== allow certwatch_t var_t:dir write;
Red Hat Enterprise Linux product, and select the selinux-policy component. Include the output of the audit2allow -w -a and audit2allow -a commands in such bug reports.
audit2allow -a, run the audit2allow -a -M mycertwatch command as the Linux root user to create custom module. The -M option creates a Type Enforcement file (.te) with the name specified with -M, in your current working directory:
# audit2allow -a -M mycertwatch ******************** IMPORTANT *********************** To make this policy package active, execute: semodule -i mycertwatch.pp # ls mycertwatch.pp mycertwatch.te
audit2allow compiles the Type Enforcement rule into a policy package (.pp). To install the module, run the /usr/sbin/semodule -i mycertwatch.pp command as the Linux root user.
audit2allow may allow more access than required. It is recommended that policy created with audit2allow be posted to an SELinux list, such as fedora-selinux-list, for review. If you believe their is a bug in policy, create a bug in Red Hat Bugzilla.
grep command to narrow down the input for audit2allow. The following example demonstrates using grep to only send denials related to certwatch through audit2allow:
# grep certwatch /var/log/audit/audit.log | audit2allow -M mycertwatch2 ******************** IMPORTANT *********************** To make this policy package active, execute: # /usr/sbin/semodule -i mycertwatch2.pp
audit2allow to build policy modules.
[12]
Files in /etc/selinux/targeted/contexts/files/ define contexts for files and directories. Files in this directory are read by restorecon and setfiles to restore files and directories to their default contexts.
[13]
The semanage port -a command adds an entry to the /etc/selinux/targeted/modules/active/ports.local file. Note: by default, this file can only be viewed by the Linux root user.
[14] From the ausearch(8) manual page, as shipped with the audit package in Red Hat Enterprise Linux 6.
[15] From the ausearch(8) manual page, as shipped with the audit package in Red Hat Enterprise Linux 6.
[16] From the aureport(8) manual page, as shipped with the audit package in Red Hat Enterprise Linux 6.
[17] From the audit2allow(1) manual page, as shipped with the policycoreutils package in Red Hat Enterprise Linux 6.
| Revision History | |||
|---|---|---|---|
| Revision 1.9 | Wed Mar 3 2010 | ||
| |||