2.4. PAM and Administrative Credential Caching
A number of graphical administrative tools in Red Hat Enterprise Linux provide users with elevated privileges for up to five minutes using the pam_timestamp.so module. It is important to understand how this mechanism works, because a user who walks away from a terminal while pam_timestamp.so is in effect leaves the machine open to manipulation by anyone with physical access to the console.
In the PAM timestamp scheme, the graphical administrative application prompts the user for the root password when it is launched. When the user has been authenticated, the pam_timestamp.so module creates a timestamp file. By default, this is created in the /var/run/sudo/ directory. If the timestamp file already exists, graphical administrative programs do not prompt for a password. Instead, the pam_timestamp.so module freshens the timestamp file, reserving an extra five minutes of unchallenged administrative access for the user.
You can verify the actual state of the timestamp file by inspecting the file in the /var/run/sudo/user directory. For the desktop, the relevant file is unknown:root. If it is present and its timestamp is less than five minutes old, the credentials are valid.
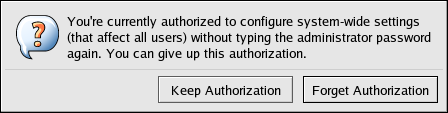
The existence of the timestamp file is indicated by an authentication icon, which appears in the notification area of the panel.
2.4.1. Removing the Timestamp File
Before abandoning a console where a PAM timestamp is active, it is recommended that the timestamp file be destroyed. To do this from a graphical environment, click the authentication icon on the panel. This causes a dialog box to appear. Click the Forget Authorization button to destroy the active timestamp file.
The PAM timestamp file has some important characteristics:
If logged in to the system remotely using ssh, use the /sbin/pam_timestamp_check -k root command to destroy the timestamp file.
Run the /sbin/pam_timestamp_check -k root command from the same terminal window where the privileged application was launched.
The logged in user who originally invoked the pam_timestamp.so module must be the user who runs the /sbin/pam_timestamp_check -k command. Do not run this command as root.
Killing the credentials on the desktop without using the Forget Authorization action on the icon can be done with the /sbin/pam_timestamp_chec command.
/sbin/pam_timestamp_check -k root </dev/null >/dev/null 2>/dev/null
Any other method only removes the credentials from the pty where the command was run.
Refer to the pam_timestamp_check man page for more information about destroying the timestamp file using pam_timestamp_check.
2.4.2. Common pam_timestamp Directives
The pam_timestamp.so module accepts several directives, with two used most commonly:
timestamp_timeout — Specifies the period (in seconds) for which the timestamp file is valid. The default value is 300 (five minutes).
timestampdir — Specifies the directory in which the timestamp file is stored. The default value is /var/run/sudo/.