Copyright © 2003, 2005 Thomas M. Eastep
Permission is granted to copy, distribute and/or modify this document under the terms of the GNU Free Documentation License, Version 1.2 or any later version published by the Free Software Foundation; with no Invariant Sections, with no Front-Cover, and with no Back-Cover Texts. A copy of the license is included in the section entitled “GNU Free Documentation License”.
2007/07/19
Table of Contents
Netfilter consists of three tables: Filter, Nat and Mangle. Each table has a number of build-in chains: PREROUTING, INPUT, FORWARD, OUTPUT and POSTROUTING.
Rules in the various tables are used as follows:
- Filter
Packet filtering (rejecting, dropping or accepting packets)
- Nat
Network Address Translation including DNAT, SNAT and Masquerading
- Mangle
General packet header modification such as setting the TOS value or marking packets for policy routing and traffic shaping.
The following diagram shows how packets traverse the various builtin chains within Netfilter. Note that not all table/chain combinations are used.
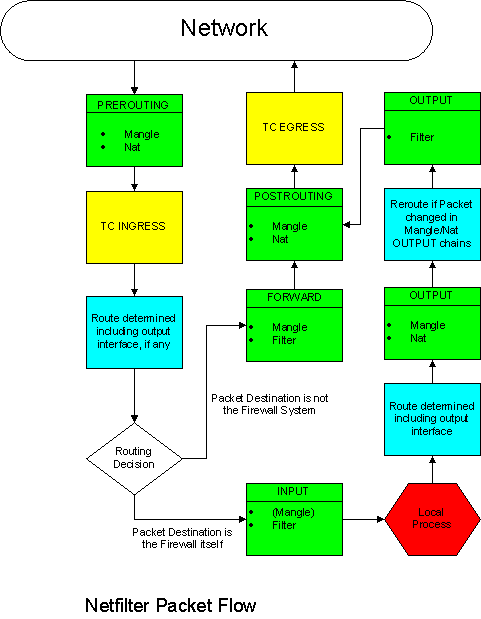
“Local Process” means a process running on the Shorewall system itself.
A more elaborate version of this flow is available here and this one contrasts the Netfilter flow with that of ipchains.
In the above diagram are boxes similar to this:
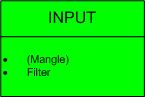
The above box gives the name of the built-in chain (INPUT) along with the names of the tables (Mangle and Filter) that the chain exists in and in the order that the chains are traversed. The above sample indicates that packets go first through the INPUT chain of the Mangle table then through the INPUT chain of the Filter table. When a chain is enclosed in parentheses, Shorewall does not use the named chain (INPUT) in that table (Mangle).
Important
Keep in mind that chains in the Nat table are only traversed for new connection requests (including those related to existing connections) while the chains in the other tables are traversed on every packet.
The above diagram should help you understand the output of “shorewall status”. You may also wish to refer to this article that describes the flow of packets through a Shorewall-generated firewall.
Here are some excerpts from “shorewall status” on a server with one interface (eth0):
[root@lists html]# shorewall status
Shorewall-1.4.7 Status at lists.shorewall.net - Mon Oct 13 12:51:13 PDT 2003
Counters reset Sat Oct 11 08:12:57 PDT 2003The first table shown is the Filter table.
Chain INPUT (policy DROP 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
679K 182M ACCEPT all -- lo * 0.0.0.0/0 0.0.0.0/0
785K 93M accounting all -- * * 0.0.0.0/0 0.0.0.0/0
0 0 DROP !icmp -- * * 0.0.0.0/0 0.0.0.0/0 state INVALIDThe following rule indicates that all traffic destined for the firewall that comes into the firewall on eth0 is passed to a chain called “eth0_in”. That chain will be shown further down.
785K 93M eth0_in all -- eth0 * 0.0.0.0/0 0.0.0.0/0
0 0 common all -- * * 0.0.0.0/0 0.0.0.0/0
0 0 LOG all -- * * 0.0.0.0/0 0.0.0.0/0 LOG flags 0 level 6 prefix `Shorewall:INPUT:REJECT:'
0 0 reject all -- * * 0.0.0.0/0 0.0.0.0/0
Chain FORWARD (policy DROP 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
0 0 accounting all -- * * 0.0.0.0/0 0.0.0.0/0
0 0 DROP !icmp -- * * 0.0.0.0/0 0.0.0.0/0 state INVALID
0 0 eth0_fwd all -- eth0 * 0.0.0.0/0 0.0.0.0/0
0 0 common all -- * * 0.0.0.0/0 0.0.0.0/0
0 0 LOG all -- * * 0.0.0.0/0 0.0.0.0/0 LOG flags 0 level 6 prefix `Shorewall:FORWARD:REJECT:'
0 0 reject all -- * * 0.0.0.0/0 0.0.0.0/0
Chain OUTPUT (policy DROP 1 packets, 60 bytes)
pkts bytes target prot opt in out source destination
679K 182M ACCEPT all -- * lo 0.0.0.0/0 0.0.0.0/0
922K 618M accounting all -- * * 0.0.0.0/0 0.0.0.0/0
0 0 DROP !icmp -- * * 0.0.0.0/0 0.0.0.0/0 state INVALID
922K 618M fw2net all -- * eth0 0.0.0.0/0 0.0.0.0/0
0 0 common all -- * * 0.0.0.0/0 0.0.0.0/0
0 0 LOG all -- * * 0.0.0.0/0 0.0.0.0/0 LOG flags 0 level 6 prefix `Shorewall:OUTPUT:REJECT:'
0 0 reject all -- * * 0.0.0.0/0 0.0.0.0/0Here is the eth0_in chain:
Chain eth0_in (1 references) pkts bytes target prot opt in out source destination 785K 93M dynamic all -- * * 0.0.0.0/0 0.0.0.0/0 785K 93M net2fw all -- * * 0.0.0.0/0 0.0.0.0/0
The “dynamic” chain above is where dynamic blacklisting is done.
Next comes the Nat table:
NAT Table Chain PREROUTING (policy ACCEPT 182K packets, 12M bytes) pkts bytes target prot opt in out source destination 20005 1314K net_dnat all -- eth0 * 0.0.0.0/0 0.0.0.0/0 Chain POSTROUTING (policy ACCEPT 678K packets, 44M bytes) pkts bytes target prot opt in out source destination Chain OUTPUT (policy ACCEPT 678K packets, 44M bytes) pkts bytes target prot opt in out source destination Chain net_dnat (1 references) pkts bytes target prot opt in out source destination 638 32968 REDIRECT tcp -- * * 0.0.0.0/0 !206.124.146.177 tcp dpt:80 redir ports 3128
And finally, the Mangle table:
Mangle Table
Chain PREROUTING (policy ACCEPT 14M packets, 2403M bytes)
pkts bytes target prot opt in out source destination
1464K 275M pretos all -- * * 0.0.0.0/0 0.0.0.0/0
Chain INPUT (policy ACCEPT 14M packets, 2403M bytes)
pkts bytes target prot opt in out source destination
Chain FORWARD (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
Chain OUTPUT (policy ACCEPT 15M packets, 7188M bytes)
pkts bytes target prot opt in out source destination
1601K 800M outtos all -- * * 0.0.0.0/0 0.0.0.0/0
Chain POSTROUTING (policy ACCEPT 15M packets, 7188M bytes)
pkts bytes target prot opt in out source destination
Chain outtos (1 references)
pkts bytes target prot opt in out source destination
0 0 TOS tcp -- * * 0.0.0.0/0 0.0.0.0/0 tcp dpt:22 TOS set 0x10
315K 311M TOS tcp -- * * 0.0.0.0/0 0.0.0.0/0 tcp spt:22 TOS set 0x10
0 0 TOS tcp -- * * 0.0.0.0/0 0.0.0.0/0 tcp dpt:21 TOS set 0x10
683 59143 TOS tcp -- * * 0.0.0.0/0 0.0.0.0/0 tcp spt:21 TOS set 0x10
3667 5357K TOS tcp -- * * 0.0.0.0/0 0.0.0.0/0 tcp spt:20 TOS set 0x08
0 0 TOS tcp -- * * 0.0.0.0/0 0.0.0.0/0 tcp dpt:20 TOS set 0x08
Chain pretos (1 references)
pkts bytes target prot opt in out source destination
271K 15M TOS tcp -- * * 0.0.0.0/0 0.0.0.0/0 tcp dpt:22 TOS set 0x10
0 0 TOS tcp -- * * 0.0.0.0/0 0.0.0.0/0 tcp spt:22 TOS set 0x10
730 41538 TOS tcp -- * * 0.0.0.0/0 0.0.0.0/0 tcp dpt:21 TOS set 0x10
0 0 TOS tcp -- * * 0.0.0.0/0 0.0.0.0/0 tcp spt:21 TOS set 0x10
0 0 TOS tcp -- * * 0.0.0.0/0 0.0.0.0/0 tcp spt:20 TOS set 0x08
2065 111K TOS tcp -- * * 0.0.0.0/0 0.0.0.0/0 tcp dpt:20 TOS set 0x08