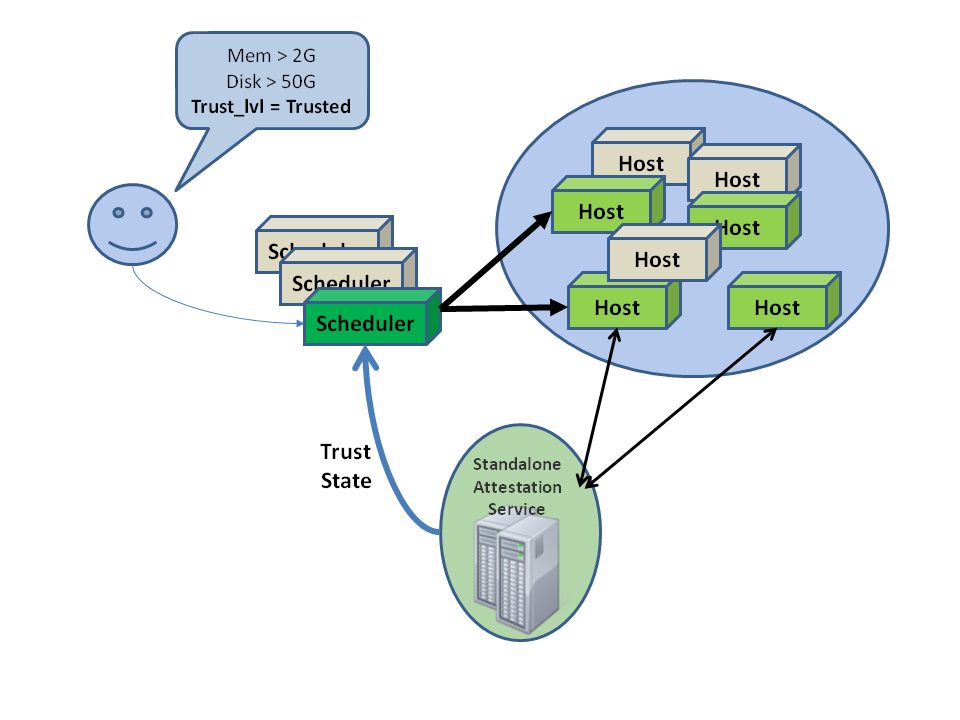
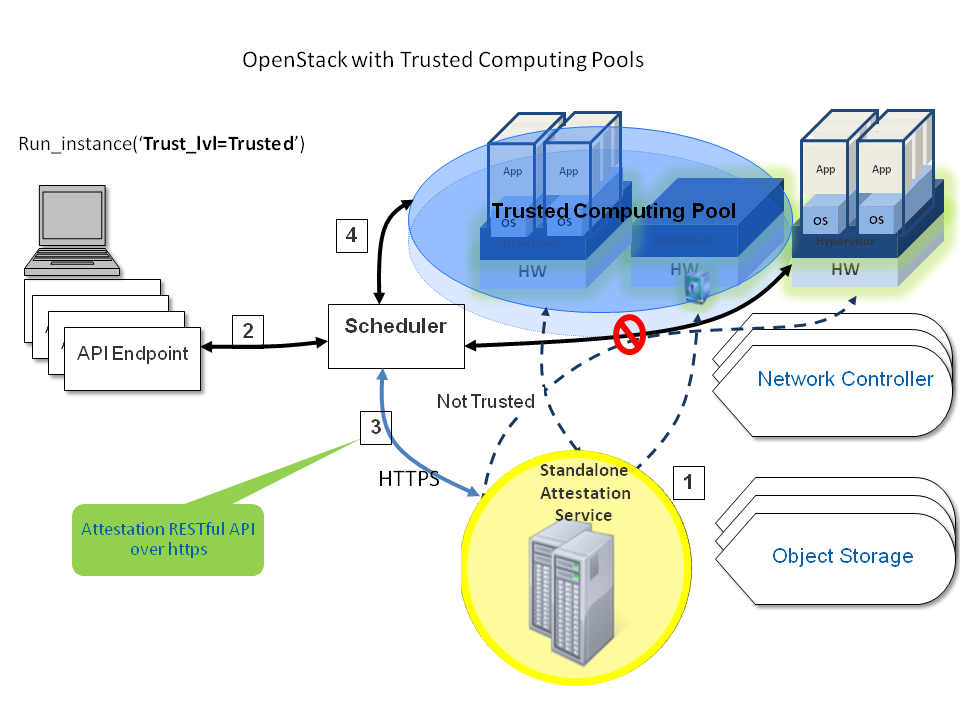
Trusted compute pools enable administrators to designate a group of compute hosts as "trusted". These hosts use hardware-based security features, such as Intel's Trusted Execution Technology (TXT), to provide an additional level of security. Combined with an external standalone web-based remote attestation server, cloud providers can ensure that the compute node is running software with verified measurements, thus they can establish the foundation for the secure cloud stack. Through the Trusted Computing Pools, cloud subscribers can request services to be run on verified compute nodes.
The remote attestation server performs node verification through the following steps:
Compute nodes boot with Intel TXT technology enabled.
The compute node's BIOS, hypervisor and OS are measured.
These measured data is sent to the attestation server when challenged by attestation server.
The attestation server verifies those measurements against good/known database to determine nodes' trustworthiness.
A description of how to set up an attestation service is beyond the scope of this document. See the Open Attestation project for an open source project that can be used to implement an attestation service.
The Compute service must be configured to with the connection information for the attestation
service. The connection information is specified in the
trusted_computing section of nova.conf. Specify the following
parameters in this section.
- server
Hostname or IP address of the host that runs the attestation service
- port
HTTPS port for the attestation service
- server_ca_file
Certificate file used to verify the attestation server's identity.
- api_url
The attestation service URL path.
- auth_blob
An authentication blob, which is required by the attestation service.
Add the following lines to /etc/nova/nova.conf in
the DEFAULT and trusted_computing sections to
enable scheduling support for Trusted Compute Pools, and edit the details of the
trusted_computing section based on the details of your
attestation
service.
[DEFAULT] compute_scheduler_driver=nova.scheduler.filter_scheduler.FilterScheduler scheduler_available_filters=nova.scheduler.filters.all_filters scheduler_default_filters=AvailabilityZoneFilter,RamFilter,ComputeFilter,TrustedFilter [trusted_computing] server=10.1.71.206 port=8443 server_ca_file=/etc/nova/ssl.10.1.71.206.crt # If using OAT v1.5, use this api_url: api_url=/AttestationService/resources # If using OAT pre-v1.5, use this api_url: #api_url=/OpenAttestationWebServices/V1.0 auth_blob=i-am-openstack
Restart the nova-compute and nova-scheduler services after making these changes.
| Configuration option=Default value | (Type) Description |
| attestation_api_url=/OpenAttestationWebServices/V1.0 | (StrOpt)attestation web API URL |
| attestation_auth_blob=None | (StrOpt)attestation authorization blob - must change |
| attestation_auth_timeout=60 | (IntOpt)Attestation status cache valid period length |
| attestation_port=8443 | (StrOpt)attestation server port |
| attestation_server=None | (StrOpt)attestation server http |
| attestation_server_ca_file=None | (StrOpt)attestation server Cert file for Identity verification |
One or more flavors must be configured as "trusted". Users can then request trusted nodes by specifying one of these trusted flavors when booting a new instance. Use the nova-manage instance_type set_key command to set a flavor as trusted. For example, to set the m1.tiny flavor as trusted:
# nova-manage instance_type set_key m1.tiny trust:trusted_host trusted
A user can request that their instance runs on a trusted host by specifying a trusted flavor when invoking the nova boot command.